
The agentic SOC category that started as a single claim (AI that automates Tier-1 triage) has fractured into platforms with incompatible architectural premises about where the security operations problem actually lives. Torq is a $1.2 billion unicorn with IDC-validated enterprise outcomes. It occupies one corner of that fracture, and understanding which corner is the prerequisite to evaluating every alternative on this list.
This evaluation addresses three specific buyer starting points:
The operational context that shapes every evaluation on this list: security teams receive an average of 4,484 alerts per day, with up to 27% of analyst time consumed by false positives. Every platform here competes to solve that problem. The organizing question is what layer of the problem each platform addresses, and whether that layer is the root cause or a symptom.
Torq is an AI SOC platform built on workflow orchestration. Security teams connect their existing security stack through Torq's integration layer, define automation playbooks for common alert scenarios, and deploy Socrates (Torq's natural-language autonomous remediation interface) to handle investigation and response without manually written code for each action. IDC validated that Torq customers automate more than 95% of Tier-1 analyst tasks, with MTTR shrinking from hours to minutes in documented enterprise deployments.
What Torq does well is specific and verifiable:
Those are proof points that a competitor evaluation should acknowledge before examining architectural limits.
The pricing reality matters for teams scoping alternatives. Torq HyperSOC lists at $450,000 per year on AWS Marketplace with 12-month contracts. Gartner reviewers flag several caveats:
This is an enterprise-grade commitment with enterprise-grade operational overhead to match.
The structural ceiling is architectural, not executional. Torq automates over whatever SIEM data already exists. IDC research establishes that the average enterprise monitors only about two-thirds of its environment due to log storage economics. When a security team deploys Torq, the platform delivers faster, automated investigation across the log sources the SIEM already covers. The remaining third of the environment produces no alerts. No alerts means no Torq investigation. This is the inherited structural constraint that every orchestration-layer platform in this alternatives list shares: automation speed is capped by data completeness, and data completeness is the problem none of them solve.
The table below covers the eight most relevant Torq alternatives by primary use case, best-fit audience, pricing model, and key architectural differentiator. Torq HyperSOC is included as the baseline row so each alternative can be oriented against a known reference point.
Most platform pricing requires a sales conversation. Torq's AWS Marketplace listing is the only publicly verified price floor in this comparison.
Each platform below is evaluated on the same criteria: what it does well, where it has structural limits relative to what security teams actually need, and which buyer profile it fits best. Several of these platforms are strong for the right use case. The evaluation matches each platform's architectural premise to the operational problem it actually solves.

Tines is a no-code workflow automation platform that security teams use heavily but that serves any operational function. The storyboard builder lets practitioners build automated workflows across security, IT, fraud, and compliance without writing code. G2 lists Tines as the most-reviewed alternative to Torq in peer comparison data, with enterprise customers including Snowflake, Elastic, and Coinbase. Tines consistently earns high ease-of-use ratings and is available at price points accessible to mid-market teams that cannot commit to Torq's six-figure floor.
The structural limit is scope depth. Tines is a horizontal automation platform with security as one use case among many. It does not encode SOC-specific agent intelligence: the investigation reasoning, alert correlation logic, and Tier-1 triage behavior that domain-specific agentic platforms ship out of the box must be built by the security team using Tines' storyboard tools. Alert fatigue is redistributed into a more automated workflow, not reduced through autonomous investigation. The log coverage gap goes unaddressed. Teams get reliable process automation without agents that reason across their environment.
What you need to know:
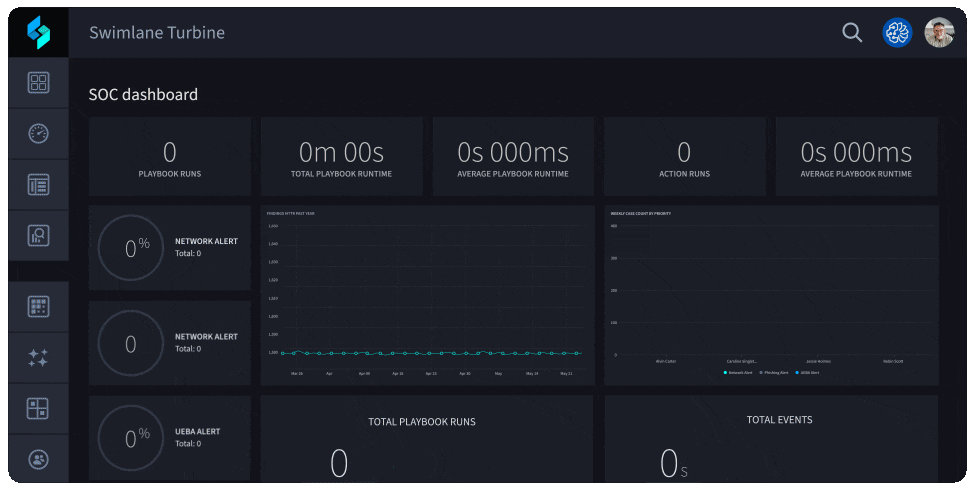
Swimlane has been a SOAR vendor since before the agentic AI wave. Turbine is their current platform, built on that established SOAR architecture with an AI triage layer on top. Gartner Peer Insights rates Turbine 4.8/5 on 120 ratings, one of the most-reviewed and highest-rated SOAR alternatives in the market. For organizations currently running IBM QRadar SOAR, Cortex XSOAR, or FortiSOAR that want to add AI triage without adopting a fully rearchitected platform, Turbine is a lower-disruption path. Playbook depth and workflow customization are strengths that newer AI-native platforms sometimes lack.
The architectural constraint is the playbook model itself. SOAR automates pre-defined playbooks. Agentic platforms reason across novel alert scenarios without requiring a playbook written in advance for each one. For teams whose alert complexity has outpaced their playbook library, Turbine delivers a better-executed version of the same structural constraint rather than an architectural escape from it. The AI triage layer helps prioritize which playbook fires, but the investigation logic still depends on what a human anticipated and encoded.
What you need to know:

Splunk SOAR ships with Splunk Enterprise Security as the native orchestration and automation layer. For organizations where Splunk is the SIEM of record, it provides an integrated automation path without introducing a new vendor. Alert data, case management, and playbook execution run within the same platform. Licensing is often bundled with existing Splunk Enterprise Security contracts, making it the lowest incremental-cost path to SOC automation for current Splunk shops.
Splunk SOAR's strength is also its constraint. It is a Splunk-native tool that adds automation value primarily within the Splunk data perimeter. Organizations running multi-SIEM environments, data lakes outside Splunk, or cloud-native log stores will find that Splunk SOAR's automation is bounded by what Splunk can already see. The platform also inherits Splunk's traditional log storage economics: high-volume ingestion at standard Splunk pricing reproduces the same coverage tradeoffs that IDC identifies in the broader enterprise SIEM market. Every log source excluded for cost reasons is a log source with zero automation coverage, regardless of how capable the SOAR layer is.
What you need to know:

Cortex XSOAR is Palo Alto Networks' SOAR product, integrated into the Cortex XDR extended detection and response platform. Organizations with meaningful Palo Alto investments (next-generation firewalls, Cortex XDR for endpoint, Prisma Cloud) get native integration depth that third-party SOAR vendors cannot replicate through API connections alone. Investigation workflows pull directly from Cortex XDR detections, firewall log data, and endpoint telemetry without the API integration overhead that Torq requires.
The tradeoff is ecosystem lock-in. Cortex XSOAR is purpose-built for Palo Alto Networks environments. Teams running mixed security stacks (SentinelOne for endpoints, Elastic for log storage, non-Palo Alto network infrastructure) will find the native integration advantage disappears as soon as investigation needs cross the ecosystem boundary.
The platform does not address log coverage gaps: it automates over whatever Cortex XDR and connected SIEM sources already see, with no federated search or search-in-place capability for log sources outside the Palo Alto ecosystem.
What you need to know:

Intezer has processed more than 25 million security alerts across live enterprise SOC environments as of 2025, achieving a less than 2% escalation rate on all investigated alerts. Fewer than two in every 100 alerts require human review. The focus is deliberately narrow: investigate alerts autonomously, at machine scale, with investigation fidelity that generalist orchestration platforms do not match. For organizations that want best-in-class investigation accuracy without paying for a broader workflow automation platform, Intezer is a legitimate choice.
The scope boundary is explicit. Intezer is a specialist tool for alert investigation. Response automation, playbook management, cross-functional workflow coordination, and compliance evidence collection fall outside its core. It also does not address the upstream data layer: if log sources are excluded from SIEM coverage for cost reasons, Intezer has no alert to investigate from those sources. The platform solves the investigation quality problem. It does not solve the visibility problem that determines how many alerts reach the investigation queue in the first place.
What you need to know:

Radiant Security combines agentic SOC capabilities with integrated log management, targeting mid-market security teams that need both visibility improvements and investigation automation in a single platform. CybersecTools ranks Radiant Agentic AI second in its list of Torq HyperSOC alternatives, reflecting its positioning as a newer-generation platform with an architectural premise closer to log-grounded agentic intelligence than traditional SOAR. Mid-market teams priced out of Torq's enterprise floor can evaluate Radiant without requiring a separate, mature SIEM as a prerequisite.
The tradeoff is market maturity. Radiant is newer to market with a smaller disclosed customer base than Torq, Tines, Splunk SOAR, or Cortex XSOAR. Teams that need enterprise-grade SLAs, proven deployment records at Fortune 500 scale, or deep existing vendor integrations across a mature security stack may find Radiant's reference list thinner than alternatives with longer track records. The integrated log management layer is a differentiator worth verifying in a proof-of-concept. Ask what log sources it covers natively, what the storage economics look like at your volume, and whether the visibility layer is architecturally comparable to purpose-built log intelligence platforms or a lightweight add-on.
What you need to know:

D3 Security's Morpheus AI layers autonomous alert triage and investigation on top of D3's established orchestration architecture. CybersecTools ranks D3 Morpheus AI third in its Torq HyperSOC alternatives list. The platform integrates with a broader set of SIEM platforms than most competitors in this space, giving multi-SIEM organizations flexibility that Splunk SOAR and Cortex XSOAR cannot match. D3's SOAR heritage means playbook depth and MITRE ATT&CK alignment are strengths for teams whose investigation workflows need to map to a specific threat framework.
The data layer constraint applies here too. D3 Morpheus AI is an orchestration and investigation tool layered over existing SIEM data. Like Torq, Tines, Swimlane, Splunk SOAR, and Cortex XSOAR, it inherits the log coverage gaps in the data it receives. The platform does not have a native data foundation layer or federated search capability. Coverage tradeoffs made at the SIEM level remain coverage tradeoffs at the D3 investigation level, regardless of how well the MITRE ATT&CK mapping organizes the alerts that do arrive.
What you need to know:

CybersecTools ranks Strike48 Platform as the number one most relevant alternative to Torq HyperSOC across 48 options evaluated. The reason is architectural: Strike48 is the only platform on this list that addresses the data foundation problem and the agent automation problem in a single architecture. The platform's federated search model (querying logs where they already live in S3, Splunk, or Elastic instead of forcing centralization into a single store) makes 100% log coverage economically viable.
Agents fire against that complete data layer rather than inheriting the coverage blind spot that IDC research identifies as the market norm.
Every other platform in this alternatives list automates over whatever log coverage already exists. Strike48's premise is that automating over incomplete data produces faster wrong answers, not better security outcomes. Mean time to detection dropped below eight minutes in early deployments. That speed is not because the automation is faster than Torq's Socrates interface. It is because agents fire against complete data and catch threats that never generated an alert on a partial-coverage SIEM. The detection speed is a consequence of the data foundation, not the orchestration layer.
The architecture behind that outcome is specific:
No single agent carries an overloaded mandate. That constraint is the architectural reason the outputs reflect the actual environment rather than statistical approximation. Every agent action produces a verifiable audit trail, so compliance teams can trace every investigation step back to specific log data.
What the platform includes:
What you need to know:
The right alternative depends on which layer of the SOC operations problem you're solving. Three paths:
Path 1: Mature SIEM coverage, need to automate the triage layer. If the security team monitors close to 100% of its environment through an existing SIEM and the primary pain is alert volume overwhelming analyst capacity, several platforms on this list are appropriate:
All platforms in Path 1 inherit existing log coverage gaps. If coverage is complete, that constraint does not apply. If coverage was set by a storage budget rather than a risk analysis, Path 2 applies.
Path 2: Log coverage gaps are limiting security outcomes. If the security team monitors less than 100% of its environment because SIEM storage economics made full coverage cost-prohibitive, no orchestration-layer platform resolves the root problem. Faster automation over incomplete data means faster wrong answers. Every platform in Path 1 raises the automation ceiling of whatever log coverage already exists, but the ceiling is still there:
The business case for fixing the data layer first is concrete: companies using AI and automation in security operations contained breaches nearly 100 days faster and saved an average of $2.22 million more than those without AI-driven defenses. That outcome depends on the AI having complete data to reason from.
Path 3: Cross-functional agentic workflows across security, fraud, IT operations, and compliance. If the SOC automation initiative is part of a broader push to deploy AI agents across business functions, the right platform has a flexible agent construction layer:
Torq is the right choice for Path 1 buyers with the budget, a mature and comprehensive SIEM, and dedicated automation engineering staff. This evaluation is not a verdict against Torq. It is a map of where each platform's architectural premise delivers and where it creates a ceiling.
Before committing to any platform on this list, ask one question: what percentage of your log sources are currently monitored, and was that percentage set by a risk analysis or a storage budget? If it was set by a storage budget, the data layer is the problem. Orchestration speed is not the fix.
If your AI pilot delivered faster alerts but didn't reduce the number of humans in the investigation loop, the problem is upstream from the automation layer.
See what agents can do when they fire against complete data. Get your free demo.
Q: Is there a free or lower-cost alternative to Torq HyperSOC?
A: No platform in this comparison offers a meaningful free tier for enterprise SOC use. Tines is available at price points below Torq's enterprise floor and accessible to mid-market teams. Splunk SOAR is often bundled with existing Splunk Enterprise Security licensing, making it the lowest incremental-cost path for current Splunk customers. Strike48's Pick reconnaissance tool is open source and free, but the full agentic log intelligence platform is enterprise pricing. The lowest-cost platform and the right platform are rarely the same. Match the alternative to the operational problem, not the budget line.
Q: Can teams migrate from Torq to another platform without disrupting existing playbooks?
A: Migration friction depends on how deeply Torq playbooks have been customized and which integrations are in active use. Swimlane Turbine and D3 Morpheus AI have the deepest SOAR heritage and are best positioned to accommodate playbook migration. Tines' storyboard format differs enough from Torq's workflow model that migration typically requires rebuilding logic rather than porting it. Newer agentic platforms (Intezer, Radiant, Strike48) do not use playbook models at all. They use agent-based investigation that reasons across alert scenarios rather than executing pre-written sequences. Migrating from Torq to an agentic platform is a rearchitecting initiative, not a playbook cutover. That is often the right strategic move, but it should be scoped that way from the start.
Q: What is the difference between a SOAR platform and an agentic SOC platform?
A: SOAR platforms (Splunk SOAR, Cortex XSOAR, Swimlane Turbine, FortiSOAR) automate pre-defined playbooks. If an alert of a specific type triggers, the platform runs a defined sequence of steps in a defined order. SOAR is deterministic and requires a human to anticipate every scenario and encode the response logic in advance. Agentic SOC platforms reason across novel alert scenarios using AI agents without requiring a pre-written playbook for each alert type. SOAR handles what has been anticipated. Agentic platforms handle what has not. In a threat environment where adversaries vary their approach at machine speed, the playbook library is structurally behind the attack surface it defends.
Q: How do I know if a log coverage gap is actually affecting my security outcomes?
A: Three diagnostic questions:
IDC research establishes that the average enterprise monitors about two-thirds of its environment. Coverage gaps are the market norm.
Q: When does an agentic log intelligence platform outperform a workflow automation platform for SOC use cases?
A: Workflow automation platforms win when automation scope needs to extend across multiple business functions, when the team needs flexibility to build highly customized workflows, and when the primary problem is process speed rather than investigation accuracy. A log intelligence platform outperforms when investigation accuracy is the priority (agents reason from complete log data, not just the alert feed from a partial SIEM), when log coverage gaps are actively creating blind spots in detection, and when the team needs autonomous investigation depth rather than workflow automation breadth. The two platform types address different architectural layers. A team could run Tines for business process automation across the organization and Strike48 for SOC, fraud, and compliance operations.