.png)
The global SOAR market is valued at USD 1.87 billion in 2025 and projected to reach USD 4.42 billion by 2030 at an 18.82% CAGR. SOAR also ranks in the bottom ten security tools by user satisfaction in the 2024 SANS SOC Survey.
Gartner declared the traditional SOAR category obsolete. The market is growing and the tools are disappointing. Both are true, simultaneously.
The reason is structural. SOC teams receive an average of 4,500 alerts per day, 67% of which are ignored entirely. Millions of cybersecurity roles remain unfilled globally, reaching 4.8 million unfilled roles according to the 2024 ISC2 Cybersecurity Workforce Study. Alert volume and workforce shortfall are not cyclical. They are compounding.
This article evaluates platforms by architectural premise, not by feature count or drag-and-drop ratings. That premise determines whether the platform can solve the problem or just automate a partial view of it. A buyer comparing eight platforms without understanding the three architectural categories they represent is comparing products that answer different questions.
Key Takeaways:
Disclosure: Strike48 publishes this content and is included in this comparison. All platforms received the same evaluation structure. The architectural framework and assessments below apply the same criteria across every entry.
The dissatisfaction reflects a structural ceiling in how first-generation SOAR tools were architected, not a failure of demand for what SOAR was trying to do. SOAR was built to solve a real problem: alert volumes that exceed human bandwidth. That problem has gotten worse, not better. Three structural factors explain why the tools keep disappointing even as the market keeps growing.
Every SOAR platform on the market automates whatever alert stream the SIEM produces. When IDC research shows the average enterprise monitors only about two-thirds of its environment due to log storage cost constraints, SOAR inherits every one of those blind spots. Automation currently helps with only 17% of alerts. 67% of all alerts are ignored entirely regardless of whether SOAR is deployed. Faster processing of an incomplete alert stream does not close the security gap. It accelerates the visible portion while the unmonitored third of the environment stays dark.
The demand side is real and getting worse. SOC teams cannot hire their way out of a 4.8 million person workforce gap that widened 26.2% in a single year. The average security employee is doing the work of 1.7 people. That pressure makes automation a structural necessity, which is why the market keeps growing even as the tools disappoint the teams deploying them.
Early SOAR required custom Python scripting and painstaking integration work per tool and use case. Low-code platforms reduced that burden, but playbook maintenance overhead still grows 15 to 20% annually as APIs change and integrations break silently. Security teams already managing live alert queues cannot dedicate the engineering hours required to keep automations current. The result is playbook rot: automations that worked at deployment gradually degrade as the tool ecosystem beneath them evolves.
Buyers evaluating SOAR platforms in 2026 are choosing between platforms built on different architectural premises about where the problem actually lives.
Three categories define the SOAR market in 2026: legacy SOAR, workflow automation platforms, and AI SOC agent platforms. They represent fundamentally different assumptions about what is broken in security operations. A buyer who treats them as price tiers will end up comparing platforms that answer different questions.
Cortex XSOAR, Splunk SOAR, and IBM QRadar SOAR built deep integration ecosystems over a decade-plus: hundreds of tool connectors, complex branching playbook logic, and enterprise-grade case management. They are production-hardened in environments running 50 or more security tools, which is the average for enterprises according to IDC.
Their core model connects to those tools, receives alerts from the SIEM, and executes predefined response workflows. Every legacy SOAR platform inherits the data coverage of the SIEM beneath it. If the SIEM monitors two-thirds of the environment, the SOAR playbooks process alerts from two-thirds of the environment. No playbook fires on a log source the SIEM never collected. The sophistication of the orchestration layer does not change the coverage of the data layer.
Implementation and maintenance complexity show up consistently in user reviews: steep learning curves, heavy reliance on engineering resources to build and maintain playbooks, and growing technical debt as tool integrations evolve. Teams that deploy legacy SOAR should budget for at least one dedicated SOAR engineer per 200 playbooks in production, because playbook maintenance is not a one-time cost.
Swimlane Turbine and FortiSOAR cut the engineering burden of legacy SOAR by 60 to 70% for initial playbook creation. Drag-and-drop builders, AI-assisted playbook creation, and faster time-to-first-automation made SOAR accessible to teams without dedicated automation engineering staff.
Reducing the authoring burden did not solve the underlying problem. Low-code makes playbooks easier to build, not more effective over incomplete data. These platforms still rely on deterministic logic and inherit the same data visibility constraints as their predecessors. A drag-and-drop playbook that fires on a phishing alert is useless if the email log source feeding that alert was excluded from the SIEM to save on ingestion costs. For teams where the core failure mode is that existing playbooks cover too small a fraction of the alert volume, a better interface does not change the math.
Agentic platforms deploy AI agents that investigate, reason across log sources, and act autonomously rather than following predetermined decision trees. The distinction is operationally significant: playbooks are brittle at the edges because novel alert types fall through deterministic branches. Agents reason about situations they have not been pre-programmed to handle, which means they can investigate the 83% of alerts that SOAR currently ignores.
There is a critical sub-distinction within this category. AI agents that fire against a two-thirds-monitored environment still produce confident outputs about an incomplete picture. The platforms that address both the reasoning layer and the data foundation layer represent the highest ceiling in the category. Strike48 is the defining example of a platform that treats full log visibility as a prerequisite to deploying agents. A buyer evaluating Cortex XSOAR against Strike48 is comparing platforms built on different premises about whether the data problem is within scope.
Before the individual platform reviews, the table below maps each platform across the criteria that matter most when SOC teams are evaluating options.
The rightmost column is the most strategically consequential criterion in this table. Every platform in the first six rows automates faster over whatever the SIEM already covers. The question is what fraction of the environment that represents.
The reviews below follow a consistent structure: what the platform does, where it performs well, where the structural limitations appear, and who it is built for. Each review acknowledges what the platform does well before explaining the tradeoffs.
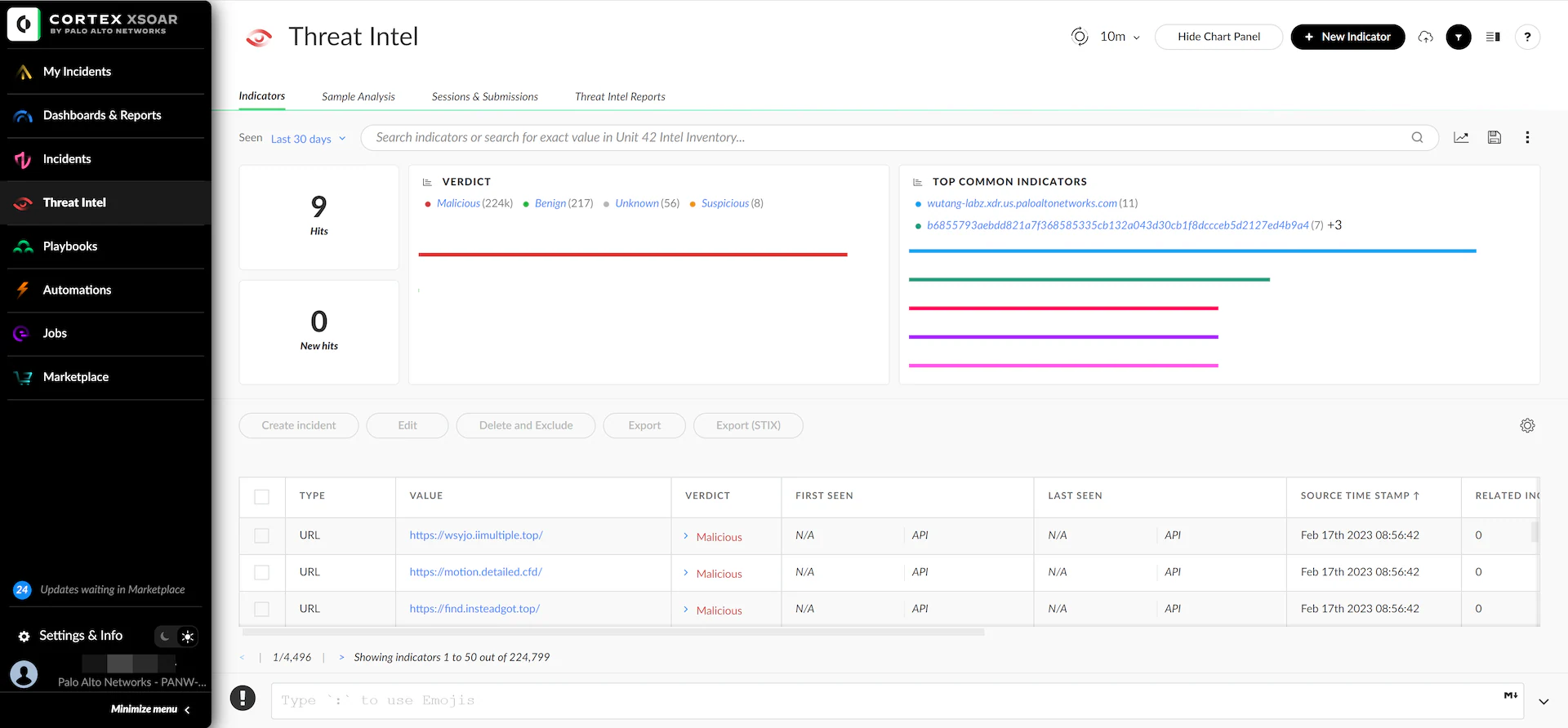
Cortex XSOAR (Palo Alto Networks) offers 900-plus integrations, making it the most widely connected enterprise SOAR platform available. Built for large enterprise security operations teams with complex, multi-tool environments, it provides mature playbook templates mapped to MITRE ATT&CK technique IDs and deep case management capabilities. Palo Alto Networks' broader security portfolio hit USD 4.8 billion in next-generation security ARR, which signals continued investment in the platform.
Integration breadth is the genuine competitive strength. For large enterprise SOCs where the security stack spans dozens of tools, Cortex XSOAR's connector library reduces custom development work that would otherwise take weeks per integration. Teams standardized on Palo Alto's broader portfolio (Cortex XDR, Prisma) benefit from native integration depth that third-party SOAR tools cannot match without additional configuration work. The playbook library is large and community-developed, giving new teams a starting point for common incident response scenarios including phishing triage, malware containment, and vulnerability prioritization.
Cortex XSOAR inherits its alert stream from the existing SIEM and does not address the data coverage problem underneath. Organizations running at partial log coverage continue to automate a partial picture. Implementation and playbook maintenance complexity consistently appear in user reviews as operational costs, even after low-code improvements to the interface. Teams evaluating Cortex XSOAR should budget for dedicated SOAR engineering resources on an ongoing basis, because the platform's depth comes with a proportional maintenance requirement.
Best suited for large enterprise SOCs with mature SIEM deployments, dedicated SOAR engineering resources, and complex multi-tool environments where integration breadth is the primary evaluation criterion. Teams already committed to the Palo Alto Networks security fabric will find the tightest native integration here.

Splunk SOAR (formerly Phantom, now part of Cisco following the USD 28 billion acquisition) delivers the tightest integration between log data and automation of any legacy offering reviewed here. For organizations already standardized on Splunk, the alert stream comes from the same platform managing the log data, which eliminates the cross-vendor configuration overhead that connecting a third-party SOAR requires.
The playbook library is extensive, and the Splunk ecosystem provides a wide base for extension. Research from Splunk shows organizations with advanced GenAI programs reduced MTTD by 38% (from 34 to 21 days) and MTTR by 68% (from 5.7 to 1.8 days). These are category-level results across advanced adopters, not Splunk SOAR-specific outcomes, but they establish a credible directional case for what AI-augmented SOC operations can achieve.
Splunk SOAR's effectiveness is bounded by what Splunk indexes, which is bounded by what the organization can afford to ingest. Splunk's per-GB pricing model creates a direct tension between coverage and cost: teams that have cut log sources to manage a six- or seven-figure annual Splunk bill will find SOAR automating over the visible portion while blind spots persist in the excluded sources. Post-acquisition road map uncertainty also affects long-term planning for some buyers evaluating Cisco-Splunk integration commitments.
Best suited for organizations deeply invested in Splunk with log coverage they are satisfied with and existing Splunk operational expertise in-house.
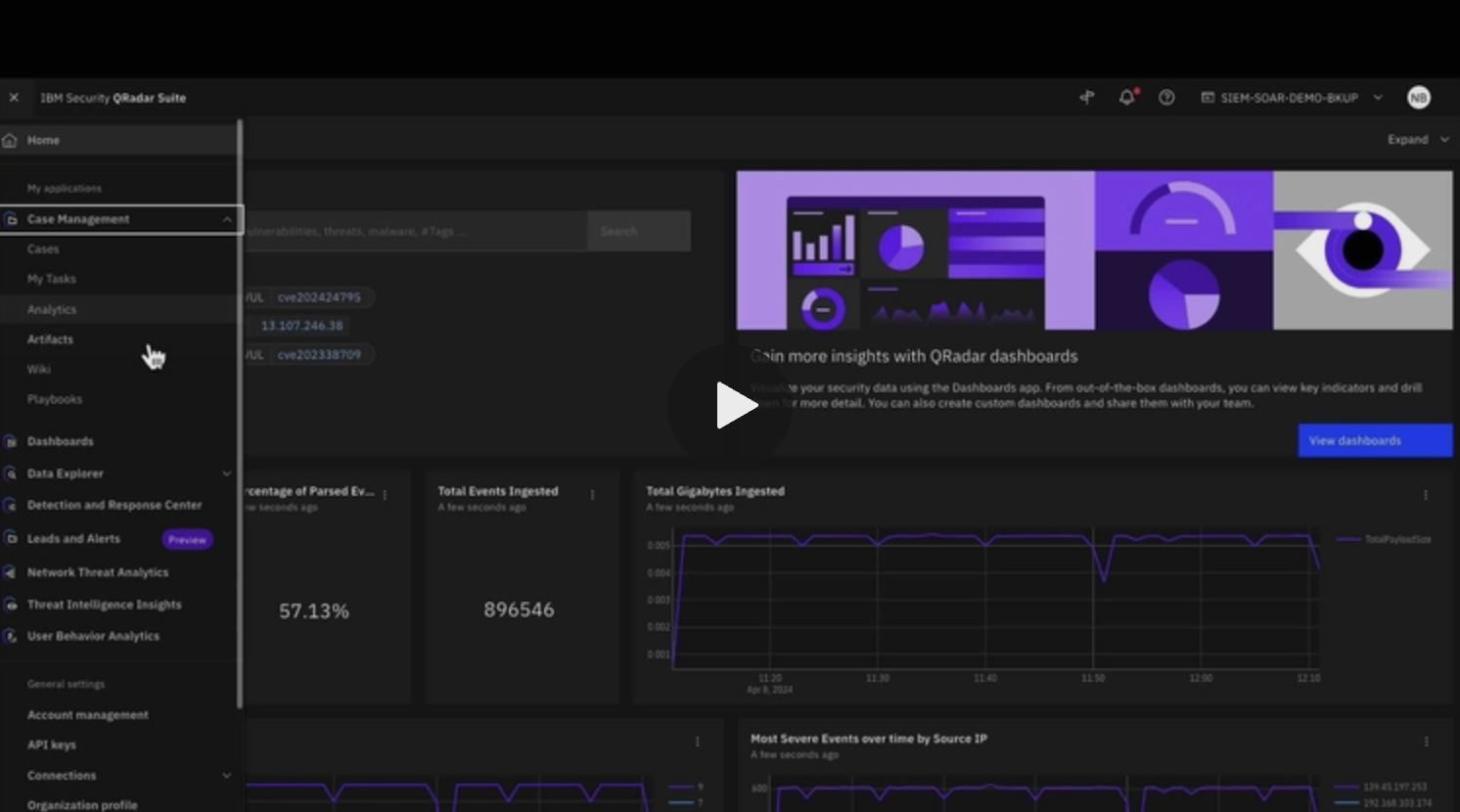
IBM QRadar SOAR provides the deepest compliance workflow automation of any platform reviewed here. Built for large-scale, regulated environments in financial services, healthcare, and government, it integrates tightly with QRadar SIEM and IBM's X-Force threat intelligence network.
Financial services and healthcare organizations operating under HIPAA, PCI-DSS, and GDPR will find QRadar SOAR's built-in compliance evidence collection and audit trail capabilities reduce the manual work of demonstrating controls during quarterly and annual audits. IBM X-Force threat intelligence enriches playbook decisions with external context that smaller vendors cannot match, including threat actor attribution and campaign tracking data that adds investigative depth to automated triage.
Implementation complexity is consistently the top complaint in user reviews. Integrations with non-IBM tools require more engineering effort than vendor documentation suggests, and the learning curve for teams without prior QRadar experience typically stretches to 8 to 12 weeks before the first production playbook is running. Like other legacy SOAR platforms, QRadar SOAR inherits the data coverage of the underlying QRadar SIEM deployment.
Best suited for large regulated enterprises with compliance-first requirements, existing QRadar deployments, and sufficient engineering resources to manage ongoing maintenance.
Microsoft Sentinel combines SIEM and SOAR in a single cloud-native platform built on Azure. Microsoft 365, Defender, and Entra ID alerts feed directly into Sentinel without custom connector work, which gives Azure-native organizations an operational advantage that third-party tools cannot replicate without weeks of configuration.
The consumption-based pricing model can be cost-effective for organizations with moderate log volumes (under 100 GB per day) compared to traditional SIEM licensing structures. The combined SIEM plus SOAR capability under one vendor reduces contracts to manage, and Sentinel fits naturally within Zero Trust architecture programs built around the Microsoft ecosystem. For organizations that have standardized on Microsoft's security stack, the native telemetry from Defender for Endpoint (EDR), Entra ID (identity), and Microsoft 365 (email and collaboration) provides a richer signal set than any third-party integration can deliver.
Consumption-based pricing at scale creates billing exposure that organizations ingesting hundreds of gigabytes daily have reported as a real budget management challenge. Cost unpredictability above the 100 GB per day threshold has led some teams to implement ingestion filters that reintroduce the same coverage tradeoffs that fixed-price SIEMs create. Non-Microsoft tool integrations require more configuration than the Azure-native integrations suggest by analogy.
Best suited for Microsoft-heavy enterprise environments standardized on Azure, Defender, and Microsoft 365 that want combined SIEM and SOAR in a single vendor relationship.
Swimlane Turbine reduced time-to-first-playbook by an estimated 60 to 70% compared to the Python-scripting requirements of legacy SOAR platforms. Its drag-and-drop interface and AI-assisted playbook building target security teams that want automation without a dedicated SOAR engineering function.
Teams that found Cortex XSOAR or Splunk SOAR too engineering-heavy have had measurable success with Turbine for standard triage and response workflows. AI-assisted authoring tools accelerate playbook creation and make basic automation accessible to analysts who don't write code. For a five-person SOC team without a dedicated automation engineer, Swimlane represents the most practical path to initial SOAR deployment among the platforms reviewed here.
Low-code reduces the authoring burden. It does not reduce the maintenance burden as integrations evolve. Playbook maintenance overhead still grows 15 to 20% annually as APIs change, tool versions update, and new use cases demand custom logic. The platform runs on top of whatever the existing SIEM monitors, inheriting the same data coverage constraints as legacy platforms. A playbook built in 30 minutes still fires on the same incomplete alert stream that a playbook requiring 30 hours of Python would.
Best suited for mid-market to enterprise SOC teams that want SOAR capabilities without dedicated SOAR engineering headcount, operating with a SIEM that covers a substantial portion of their environment.
FortiSOAR delivers the tightest vendor-native integration of any platform reviewed here for organizations already running Fortinet infrastructure. Within the Fortinet security fabric (FortiGate, FortiSIEM, FortiEDR), standard incident response workflows operate with minimal connector configuration because the tools share a common data model.
Organizations running FortiGate firewalls, FortiSIEM, and FortiEDR get an integration stack that would require weeks of custom connector work to replicate by connecting a third-party SOAR to the same tools. The licensing model benefits teams already paying for Fortinet security products at the platform tier.
Outside of Fortinet-native environments, the integration story weakens. Third-party tool support is narrower than what Cortex XSOAR or Splunk SOAR provide, which makes FortiSOAR a poor fit for heterogeneous tool stacks. Coverage limitations inherited from the underlying SIEM apply here as they do across the legacy and workflow automation categories.
Best suited for organizations standardized on the Fortinet security fabric who want automation tightly coupled to existing Fortinet tooling.
D3 Security adds AI-assisted investigation and enrichment on top of traditional playbook orchestration, positioning its platform as "Smart SOAR." The enrichment layer adds alert context that deterministic playbooks alone cannot generate, including entity reputation scoring, behavioral baselines, and cross-source correlation that reduces the manual investigation work analysts perform before making a triage decision.
For organizations not yet ready for a fully agentic platform, D3 represents a credible intermediate position. Pre-built alert triage workflows reduce alert-to-analyst handoff time compared to traditional SOAR, and the AI enrichment means analysts receive alerts with more context attached, which compresses the time between alert arrival and disposition.
D3 operates on top of existing SIEM and log infrastructure, inheriting the same data coverage constraints as every other platform reviewed above. The AI enrichment improves what happens to alerts after they arrive. It does not address why some alerts never arrive because their log sources aren't monitored. "Smart SOAR" augments the workflow model without rethinking the data layer underneath it.
Best suited for organizations that want AI-assisted triage over their existing SIEM infrastructure as a step up from legacy playbook automation.
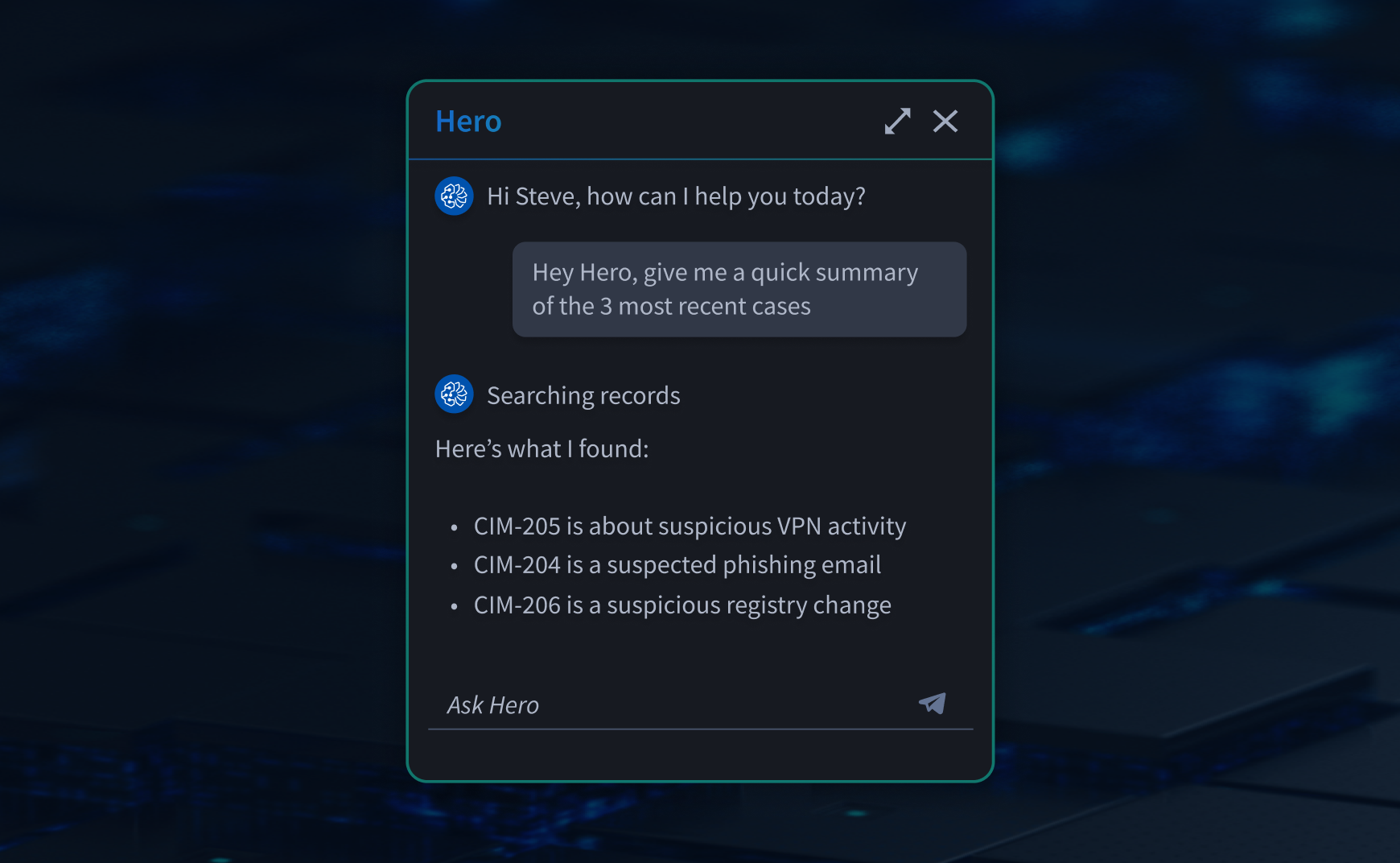
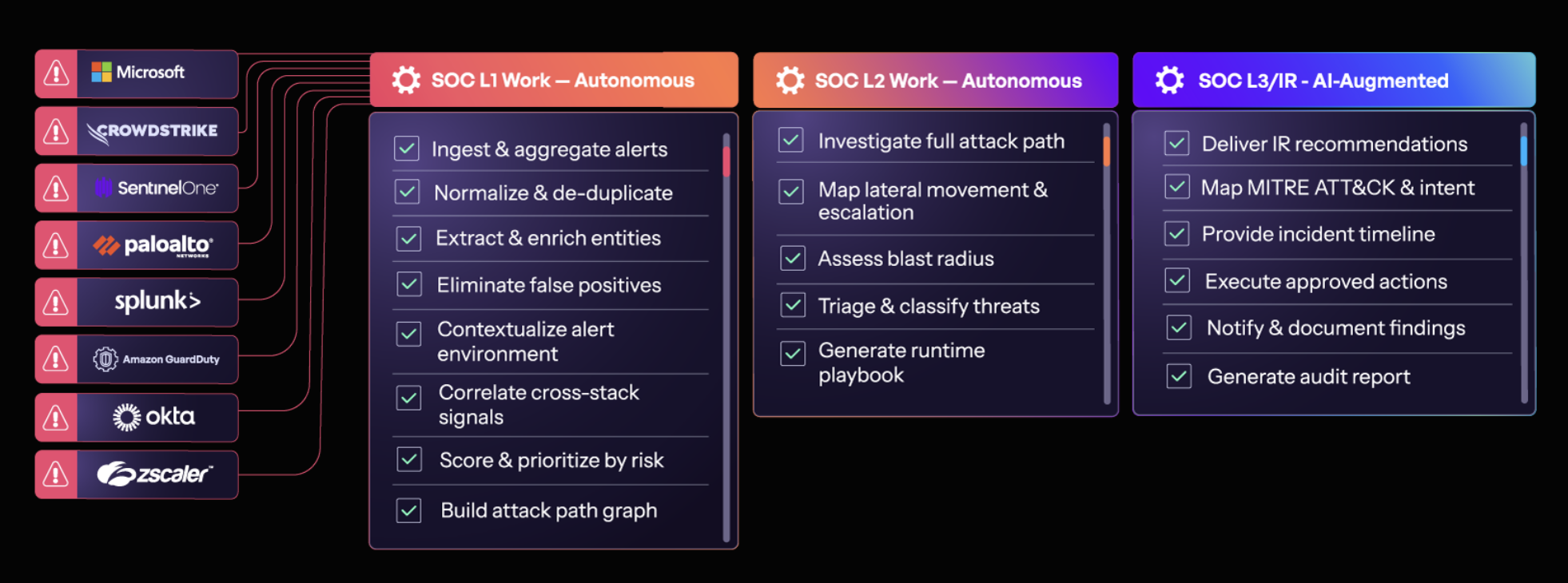
Strike48 addresses the data visibility layer before deploying any agents. A federated search architecture queries logs wherever they already live (S3, Splunk, Elastic, data lakes) rather than forcing centralization into a single index. Search-in-place connectors eliminate the forced tradeoff between log coverage and log storage cost that creates blind spots in every other platform reviewed here. Teams keep data where it sits today, with no migration required.

The micro-agent architecture assigns each agent a specific, bounded task with a defined GraphRAG (graph-based retrieval-augmented generation) knowledge graph and constrained MCP (Model Context Protocol) tool access. Agents given small, specific jobs don't hallucinate to please you. Narrow scope plus GraphRAG plus MCP tool constraints is the architectural reason why. A coordinator agent receives an alert and splits it into discrete tasks: check these IPs, pull this user's authentication history, run this behavioral baseline. Specialist agents handle each task with a constrained knowledge graph and approved tool set. Results route back to the coordinator for synthesis.
Pre-built agent packages for SOC Level 1, SOC Level 2, SOC Manager, phishing detection, fraud detection, and compliance evidence collection deploy without custom development. In early deployments, mean time to detection dropped below eight minutes. Strike48 agents uncovered active phishing campaigns that legacy SIEM tools had missed and automatically generated and validated new detection rules before real attacks occurred. Smart collection covers approximately 80% of an organization's log sources in under a day for SaaS deployments.
Strike48 is a newer platform compared to the decade-plus production histories of Cortex XSOAR or Splunk SOAR. Teams evaluating it will find fewer pre-built integrations and less documented deployment variety than legacy platforms provide. Organizations with mature, playbook-heavy SOAR environments will face a migration consideration rather than a simple addition. On-premises and air-gapped deployments require weeks to go-live rather than the minutes available for shared SaaS.
Best suited for organizations where log coverage gaps are a known, unsolved problem. Teams that have deployed AI-assisted tools and found output quality limited by incomplete data. Enterprises building agentic workflows across security, fraud, compliance, and IT operations in a single platform.
Most platforms in this category do not publish pricing, and any list prices found in independent review sites are unreliable at enterprise scale. Rather than padding this section with estimated ranges, here is what actually determines the total cost of ownership over three to five years.
Platform licensing with usage tiers (Cortex XSOAR, IBM QRadar SOAR, Swimlane Turbine) combine upfront licensing with variable costs for integrations, support tiers, professional services, and annual maintenance. Total cost of ownership consistently exceeds list price once implementation and ongoing engineering costs are included. Buyers should request explicit scoping of professional services expectations before signing, because implementation hours are where the budget variance lives.
Strike48 offers shared SaaS, isolated compute, and on-premises deployment tiers. The deployment model drives cost rather than raw log volume, which is consistent with the federated search premise that log coverage should not be constrained by storage pricing. When the pricing model does not penalize ingestion volume, coverage decisions are driven by risk rather than budget.
The more important question than the price point is what the pricing model incentivizes. Per-GB pricing incentivizes coverage tradeoffs. Per-analyst pricing incentivizes lean headcount. Platform-tier pricing requires careful scoping of hidden costs. The pricing model that aligns with a full-coverage security strategy is the one worth evaluating first.
Before finalizing any platform decision, ask one question: what percentage of your environment is your current log infrastructure actually monitoring, and how was that percentage determined?
If the answer is "we don't know," that is a data governance problem that any new automation layer will inherit. If the answer is "about two-thirds," that matches commonly reported industry benchmarks, and it means one-third of the attack surface produces no alerts that any SOAR platform can act on. If the answer is "less than half," legacy SOAR or workflow automation is automating a minority of the actual environment while the majority stays dark.
The traditional SOAR evaluation asks which platform has the best playbooks, the most integrations, and the easiest interface. The evaluation that matters in 2026 asks whether the platform addresses the data coverage problem underneath the playbooks, or inherits it. Every platform in the legacy and workflow automation categories inherits it. The emerging agentic category, at its best, addresses it.
If your current setup forces coverage tradeoffs or automation has failed to reduce human load despite the promises, see what complete log visibility plus purpose-built agents actually looks like. Request a demo.
Is SOAR dead in 2026?
No, but the traditional category definition is under real pressure. Gartner declared the SOAR category obsolete, and SOAR ranks in the bottom ten security tools by user satisfaction. The problem SOAR was built to address (alert volumes exceeding human capacity) is intensifying: 4,500 alerts per day per SOC team,4.8 million unfilled cybersecurity roles globally. What is changing is the architectural approach. Playbook-based automation is giving way to agentic investigation platforms that reason and act rather than follow predetermined decision trees.
What is the difference between SOAR and XDR?
SOAR automates security workflows across multiple tools via playbooks and integrations. XDR (Extended Detection and Response) ingests telemetry natively across endpoint, network, and cloud sources to deliver unified detection and response within a single vendor's ecosystem. SOAR is broader in tool connectivity across vendors. XDR is deeper in native telemetry integration within one vendor's stack. They frequently coexist, with XDR handling native telemetry and SOAR orchestrating responses across the broader tool environment.
How does SOAR relate to SIEM?
SIEM collects and correlates log data to surface alerts. SOAR automates the response to those alerts. SOAR's effectiveness is bounded by what the SIEM monitors: if the SIEM does not collect a log source, SOAR never receives an alert from it and no playbook fires. This dependency separates legacy SOAR architectures (which inherit whatever coverage the SIEM provides) from platforms like Strike48 that address the data layer directly before deploying automation.
What makes a SOAR platform work well for MSSPs?
Three capabilities most platforms only partially deliver: multi-tenant isolation (each client's data and automations scoped separately), investigation capacity that scales without proportional headcount growth, and audit trails that satisfy client SLA reporting requirements. Platforms with pre-built agent packages for common SOC workflows reduce time-to-value per new client onboarded and compress the engineering work of standing up client-specific automation.
How long does SOAR implementation take?
Legacy SOAR implementations (Cortex XSOAR, Splunk SOAR, IBM QRadar SOAR) typically require weeks to months for initial deployment and ongoing engineering resources for playbook development. Low-code platforms (Swimlane Turbine, FortiSOAR) reduce initial deployment time while still requiring workflow design and testing cycles. AI SOC agent platforms with pre-built packages can begin operating within minutes to hours on shared SaaS deployments. On-premises and air-gapped deployments require weeks due to infrastructure preparation. Strike48's smart collection covers approximately 80% of log sources in under a day for SaaS deployments, which means complete visibility is operational before most legacy SOAR teams have finished configuring their first ten playbooks.