It is 7 AM on a Monday. The alert queue has grown since the last shift ended.
Security teams field an average of 4,484 alerts per day and burn up to 27% of their time chasing false positives. Headcount cannot close the gap. There are an estimated 4.8 million unfilled cybersecurity roles globally. Hiring is a strategy with a hard ceiling.
“SOC automation” is not a single thing. Three architectural categories exist, and each one has a different operational ceiling. Deterministic playbook platforms execute what humans have defined. LLM-native triage tools investigate alerts from existing SIEM data. Agentic platforms run multi-step investigations and act on findings.
Three tiers of SOC automation exist, and each hits a structural wall at a different height. Knowing which wall you are buying into prevents the most expensive mistake in SOC tooling.
One prerequisite applies across all three. The average enterprise monitors only about two-thirds of its environment. The other third produces no alerts. No SOAR runs on an alert that never fires. No agent investigates a threat that never surfaces.
The “log coverage approach” column reflects how each platform handles the underlying data question, the most operationally significant variable not visible in most product comparisons.
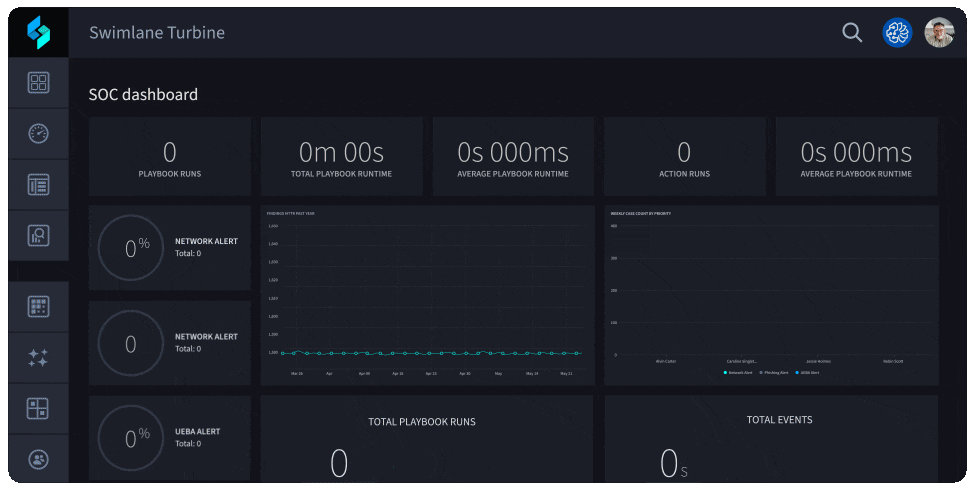
Swimlane is a low-code SOAR focused on workflow automation, case management, and cross-tool orchestration. Teams author playbooks; Swimlane executes them at scale. The Turbine acquisition added LLM-assisted playbook generation.
Best fit: SOCs with mature, documented processes and dedicated playbook engineering resources. The ceiling: Swimlane operates on alerts it receives from upstream. Alert fatigue from an incomplete SIEM is not reduced by adding a SOAR. The platform accelerates execution within a defined perimeter; it does not expand the perimeter.

Cortex XSOAR provides playbook-based automation with a catalog of 900+ integrations covering case management, threat intel aggregation, and collaborative investigation. Part of the broader Cortex platform alongside Cortex XDR.
Best fit: Large enterprise SOCs with significant Palo Alto investment running 15 to 30 connectors in production. The ceiling: Integration breadth does not address log source exclusions upstream. Playbooks for known threat patterns execute reliably; novel patterns require human investigation.
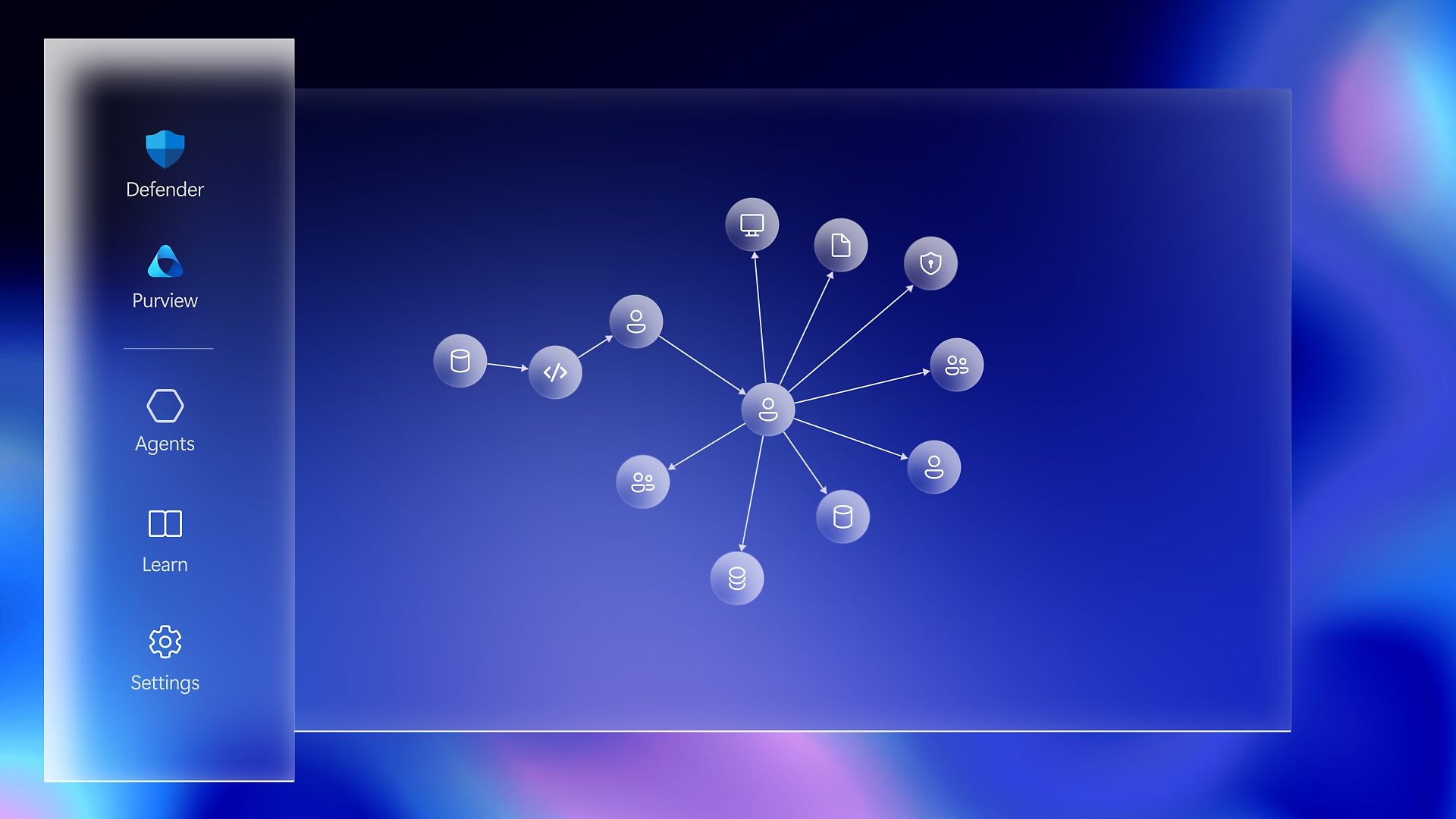
Microsoft Sentinel is a cloud-native SIEM and SOAR platform within the Azure and Microsoft Defender ecosystem. Microsoft Copilot for Security adds LLM-assisted investigation on top of the SIEM interface.
Best fit: Organizations running primarily on Azure, Microsoft 365, and the broader Microsoft security stack that want a single-vendor approach. The ceiling: Cost-per-GB log ingestion creates the same coverage tradeoffs as legacy SIEMs. At $2.46 per GB pay-as-you-go, 500 GB of daily logs force explicit choices about which sources to monitor and which to exclude. Those exclusions become structural monitoring gaps.

Formerly Splunk Phantom, Splunk SOAR is a playbook-based platform deeply integrated with Splunk Enterprise Security and Splunk Cloud.
Best fit: Organizations with significant Splunk investment, plus MSSPs running multi-tenant Splunk environments. The ceiling: Automation quality is bounded by Splunk data feeding it. Teams that excluded high-volume sources to manage indexing costs carry the same gaps into Splunk SOAR.

Intezer combines behavioral ML, LLM reasoning, and genetic malware analysis to investigate and disposition alerts. Published benchmarks claim 98% accuracy and full alert investigation coverage in under two minutes.
Best fit: Teams whose primary pain is alert volume and false positive rate, not coverage. False positive rates in enterprise SOCs frequently exceed 50%, some above 80%. The ceiling: Threats from unmonitored sources stay invisible to both the SIEM and Intezer. Forensic quality is genuinely differentiated; the coverage gap sits upstream.

Exaforce routes each alert to the right type of reasoning. Known patterns trigger deterministic automation. Anomalous behavior triggers behavioral ML. Novel or ambiguous threats trigger LLM-based reasoning. A phishing alert and a lateral movement detection require different analytical approaches.
Best fit: Enterprise SOCs processing diverse alert types across endpoint, network, identity, and cloud sources. The ceiling: Exaforce layers multi-model reasoning over existing log infrastructure. Improved reasoning applied to a structurally incomplete dataset still misses what the dataset does not contain.
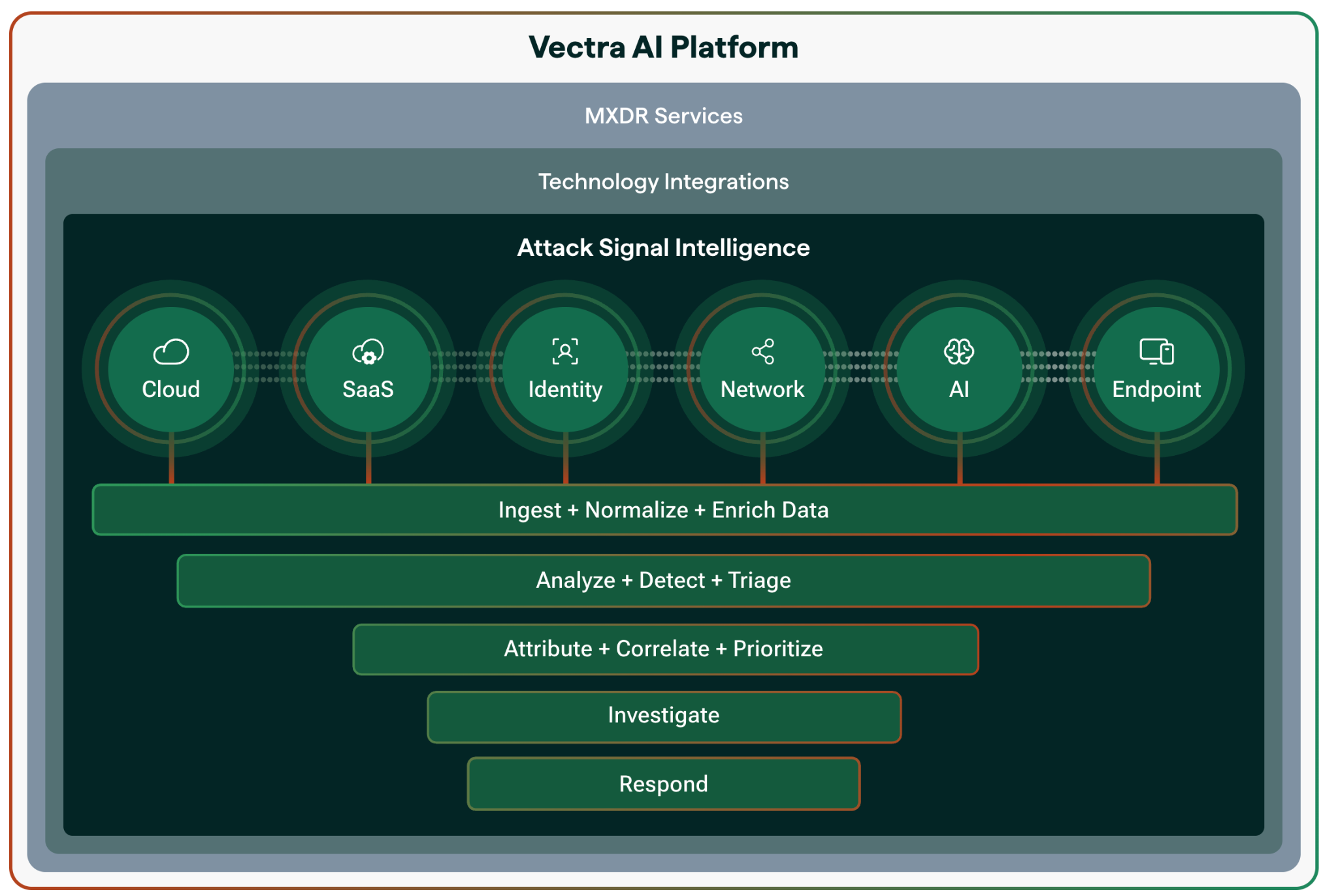
Vectra AI monitors east-west and north-south network traffic to catch attacker behavior that endpoint and SIEM analysis miss: lateral movement, command-and-control beaconing, privilege escalation across network segments. AI models run behavioral analysis on network metadata without requiring EDR agents.
Best fit: Manufacturing with SCADA, healthcare with connected medical devices, utilities with legacy control systems. The ceiling: Cloud API logs, identity telemetry, and application layer events outside the network layer are not in scope. SIEM integration partially addresses this; it does not replace complete multi-source visibility.

Stellar Cyber ingests and normalizes data from existing tools (SIEM, EDR, NDR, cloud security scanners) into a unified XDR layer. ML behavioral analytics correlate signals across the normalized pool. The average enterprise runs 28 distinct security tools with separate dashboards.
Best fit: Analysts context-switching between 20+ unintegrated dashboards. The ceiling: Stellar Cyber normalizes what existing tools produce. An EDR covering 80% of endpoints contributes 80% of endpoint visibility. A SIEM excluding high-volume sources contributes that incomplete data. Unification improves analyst workflow but does not guarantee the unified dataset is structurally complete.
Radiant Security connects to existing SIEM infrastructure and uses large language models to autonomously investigate, contextualize, and disposition alerts. AI-augmented SOCs report a 60% drop in manual triage workload compared to unassisted operations.
Best fit: Teams with high tier-1 alert volume and a well-configured SIEM that produces a quality alert stream. The ceiling: Radiant is a triage layer over existing infrastructure by design. If two-thirds of log sources are monitored, Radiant investigates the two-thirds; the rest stays outside its scope. The triage is fast. The coverage question is upstream.
Every platform above accepts existing SIEM coverage as a given constraint. Strike48 addresses the visibility prerequisite first.
Federated search and search-in-place. Strike48 reads directly from S3, Splunk, Elastic, and existing data lakes without requiring migration or duplicate storage. Agents fire against complete data, not a subset of what budget allowed the SIEM to ingest. The economic barrier that forces monitoring tradeoffs in traditional architectures dissolves at the data layer. (More on agentic log intelligence.)
Why the data foundation matters. Two-thirds of the environment monitored leaves roughly 330 potential detection signals per 1,000-alert day with zero coverage. Nothing for a SOAR to orchestrate. Nothing for an LLM to triage. Nothing for an agentic platform to investigate.
Anti-hallucination by architecture. Strike48 uses micro agents, each scoped to a specific task, that hand work off to each other like a coordinated SOC team. A coordinator agent splits an alert into discrete investigation tasks and routes each to a specialist agent with a defined knowledge graph and constrained tool set. GraphRAG persona graphs constrain what each agent knows. MCP connectors restrict what tools each agent invokes. Agents given narrow jobs with defined knowledge do not confabulate. Companies deploying AI in security operations cut breach costs by an average of $2.2 million.
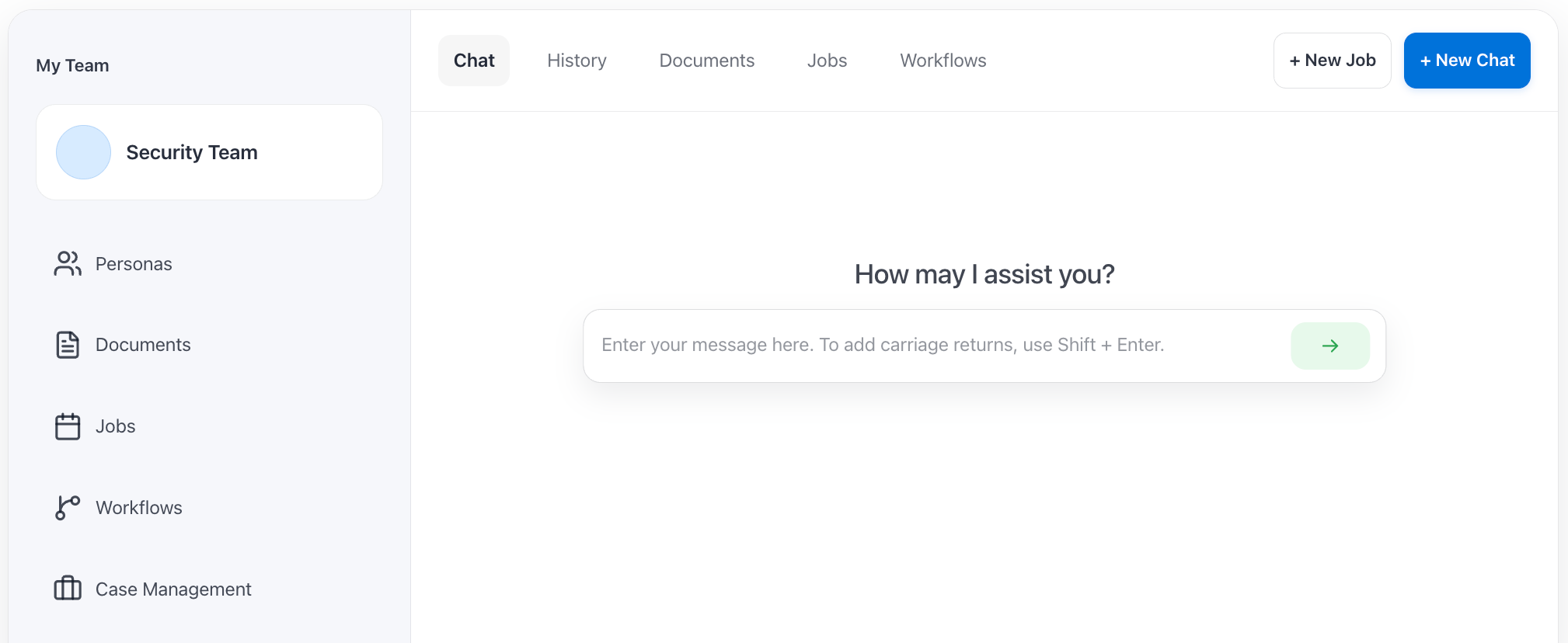
Use cases and scope. SOC Level 1 through 3 automation, phishing investigation, fraud detection, compliance evidence, and custom agent workflows built through Prospector Studio. Deployment options include shared SaaS, isolated compute, and on-premises or air-gapped environments.
These apply across every platform on this list, and every platform not on it.
For years, the standard advice was buy a SOAR and invest in playbook engineering. That approach has a ceiling. Alert volumes are growing faster than playbook libraries can expand, and the market has moved toward agentic investigation.
The reliability of agentic investigation depends on what the agents can see. The intelligence is already in your logs. The question is whether your tooling can reach all of it.
If you want to see what your agents are missing, and what changes when they reason over complete logs instead of a budget-constrained subset, that is the conversation we have most often. Walk us through your detection stack and we will run a side-by-side investigation against your data.
A platform that automates some portion of SOC investigation and response. The category spans SOAR platforms that execute pre-defined playbooks, LLM-native triage tools that investigate alerts via language model reasoning, and agentic platforms that run multi-step investigations autonomously. Architecture determines the capability ceiling, not the category label.
SOAR platforms execute playbooks humans defined in advance. Agentic platforms run the investigation themselves, handling threats no playbook anticipated. Both inherit the coverage constraints of the underlying data layer unless the platform addresses log visibility as a prerequisite. Strike48 combines federated search with autonomous micro-agent investigation in one platform.
No. Current platforms maintain human-in-the-loop controls at high-consequence decision points. Tier 1 and Tier 2 investigation volume moves to agents; analysts shift to threat hunting and decisions requiring organizational context. The IBM Cost of a Data Breach Report found AI-augmented SOCs contain breaches 108 days faster than those without.
Track five metrics from day one: MTTD, MTTR, tier 1 alert investigation coverage, false positive escalation rate, and analyst hours saved on routine triage. AI-augmented SOCs report a 50% reduction in MTTD and a 60% drop in manual triage workload. Establish baselines for at least 30 days before deployment.
Every other platform layers automation or AI reasoning on top of existing SIEM data, inheriting whatever coverage gaps that SIEM carries. Strike48 addresses the data foundation first through federated search and search-in-place, then deploys narrowly scoped micro agents against that complete dataset. Agent outputs are grounded in full environmental visibility rather than a budget-constrained subset.