.png)
If you're searching "tines competitors," you've already seen what Tines can do.
The no-code storyboard builder works. The connector library is deep. And for teams that need one automation layer across security, IT, and business operations, the platform earns its 4.8-star G2 rating across 351 reviews.
The question security teams keep running into is whether any workflow tool can solve the problem that keeps SOC teams underwater: 63% of daily security alerts go completely unaddressed because the data feeding those alerts is incomplete, and the humans reviewing them can't scale.
That requires a different evaluation. The platforms below are the ones security teams most often compare to Tines. Each solves a different piece of the problem.
Tines delivers genuine cross-functional workflow automation at enterprise scale. Deployments across Snowflake, Coinbase, GitLab, and Canva prove it works. The AI Interaction Layer launched in January 2026 added unified AI orchestration with MCP server support, human-in-the-loop controls, and audit logging for every AI action. Two-thirds of Tines customers now actively use AI features in the platform.
The ceiling shows up when security teams need more than workflow execution. Tines doesn't have a native log intelligence layer, which means it can't determine whether the data feeding your detection tools is complete. Teams building security automation on Tines are building against whatever alerts their existing infrastructure surfaces. IDC research puts the average enterprise at roughly two-thirds log environment coverage because SIEM storage costs force monitoring tradeoffs. Tines automates the visible portion. The remaining third produces no alerts and therefore no automation, which means potential attack paths with zero visibility.
That's a category boundary. The platforms below are where buyers go when they cross it.
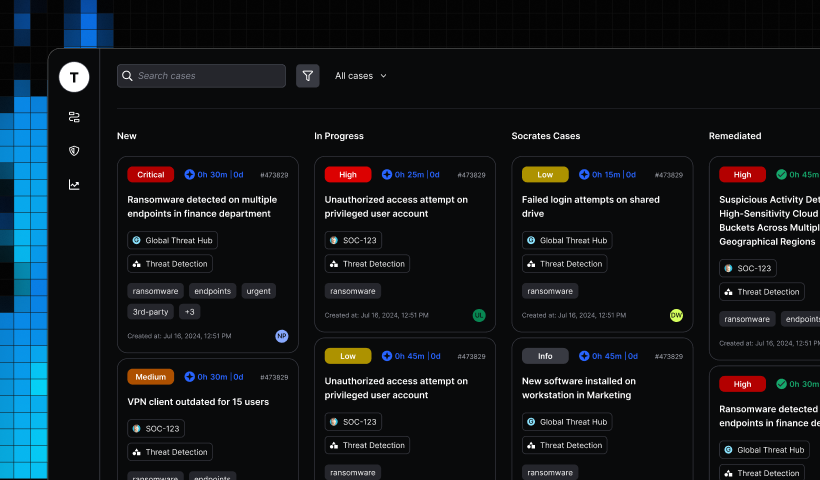
Torq has built a credible AI SOC platform with enterprise traction. The HyperSOC product and Socrates natural-language remediation engine deliver autonomous investigation, documentation, and response. A $140M Series D in January 2026 at a $1.2B valuation signals strong investor confidence. Case studies across Bloomreach, Agoda, and Kenvue show production deployments, and audit trails with manual override controls address the governance concerns that slow enterprise AI adoption.
Torq is an orchestration layer, which means it assumes the security data it automates over is complete. If the underlying environment monitors a fraction of log sources because storage economics forced the tradeoff, Torq automates the visible portion. A SOC running Torq over 70% log coverage gets faster triage on 70% of the attack surface. The other 30% generates zero alerts, zero investigations, zero response actions, regardless of how sophisticated the orchestration is.
Buyer fit: Enterprise security teams with mature SIEM coverage that need to automate existing workflows and response playbooks at scale.
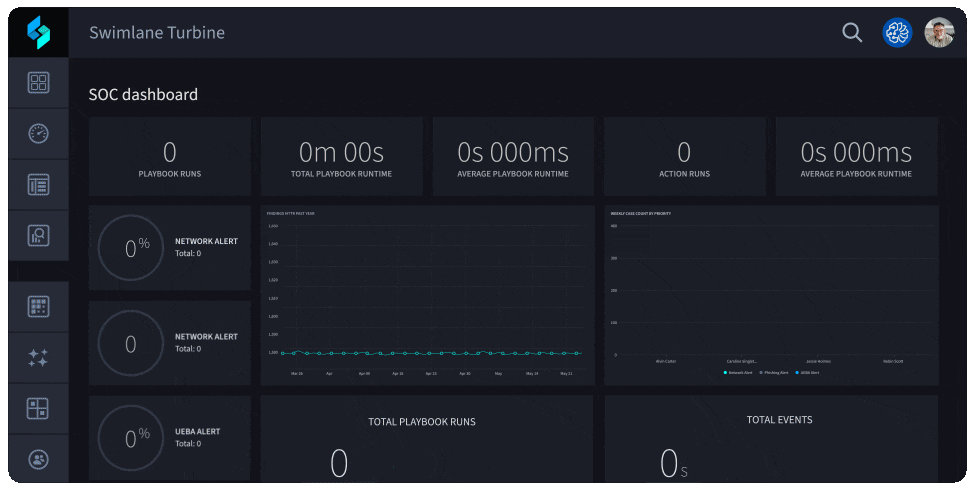
Swimlane (the product platform is called Turbine) is one of the more established SOAR-to-agentic transition platforms. More than 40 Fortune 500 companies and 26 U.S. federal agencies run Swimlane in production. The Hero AI suite now includes agentic capabilities, an agent builder, and low-code playbooks, and Intelligent Deep Agents launched in February 2026 pushed the platform further into agentic territory. Swimlane earned the #1 position in the 2025 QKS Group SPARK Matrix for SOAR for the third consecutive year.
The limitation is structural. Swimlane automates over alerts and events surfaced by existing detection infrastructure. If detection is incomplete, Swimlane has nothing to automate against the blind spots. There's no native mechanism for expanding log coverage or querying data stores outside the connected tool set, so the coverage gap persists regardless of how capable the automation becomes.
Buyer fit: Security operations teams with well-defined playbook libraries that need AI-assisted automation with a proven, mature vendor.

Splunk SOAR offers deep integration within the Splunk ecosystem (now a Cisco business unit following the $28B acquisition in March 2024). Over 300 third-party integrations and 2,800 automated actions are available via Splunkbase. Agentic AI features announced at .conf25 in September 2025 positioned Splunk as a contender in the autonomous SOC space, with Cisco Data Fabric integrations expanding the platform's reach.
The constraint is architectural and has limited Splunk for years. Splunk's parse-at-ingestion model requires teams to decide which log sources to parse and retain before they know which sources matter. Storage costs scale linearly with volume, which means teams routinely exclude log sources that generate high volume but uncertain value. Those excluded sources still carry risk. Faster playbook execution over incomplete data doesn't reduce mean time to detection for the log sources that were too expensive to ingest.
Buyer fit: Organizations standardized on Splunk as their primary SIEM that want automation within that ecosystem without introducing new data infrastructure.
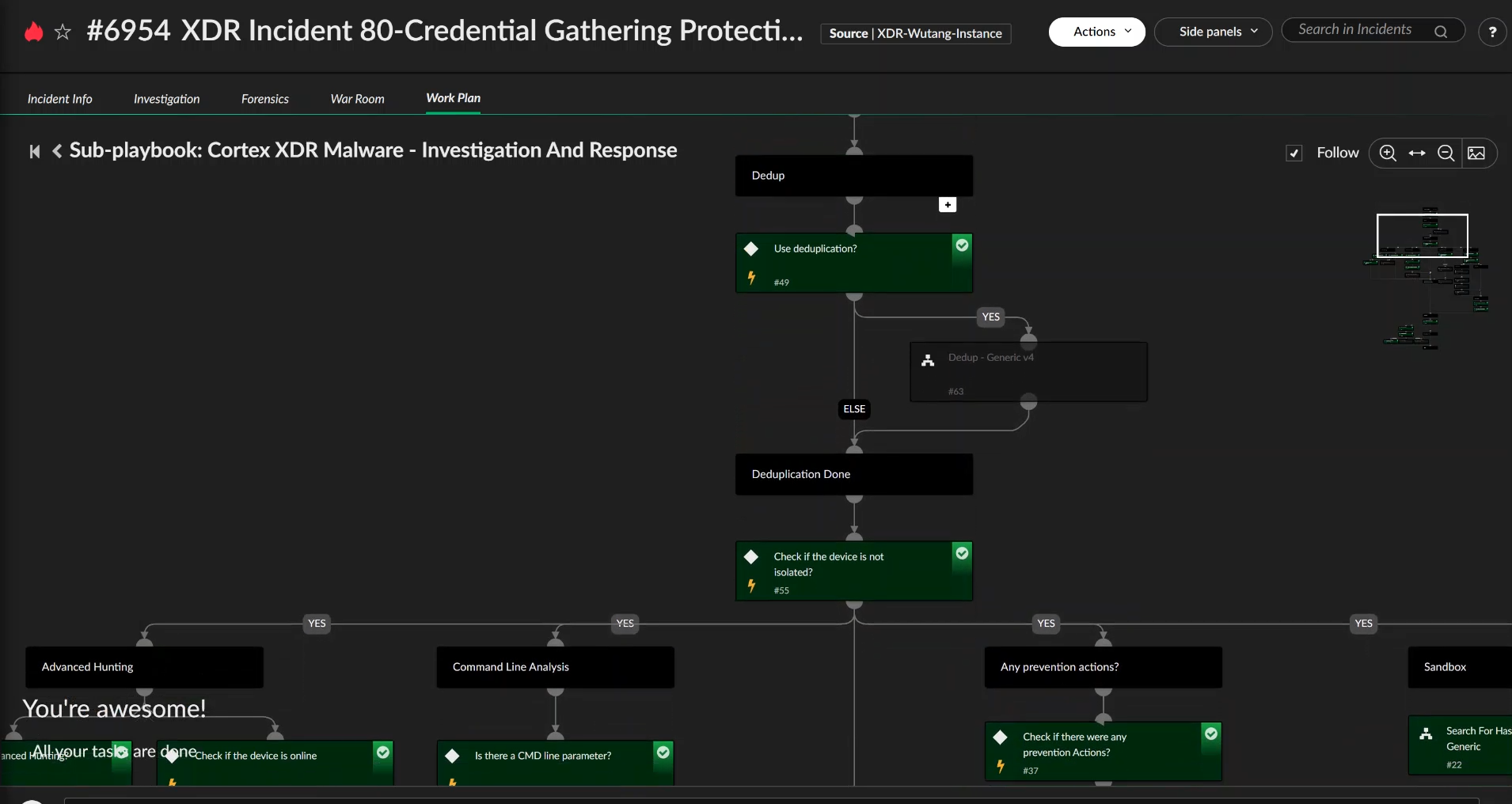
Palo Alto Networks announced Cortex AgentiX in October 2025 as the successor to Cortex XSOAR, shifting from playbook-driven automation to agentic AI with autonomous investigation and decision-making. XSOAR professional services SKUs simultaneously entered end-of-sale. For teams already in the Palo Alto ecosystem, the Cortex suite delivers native automation with unified case management.
Teams evaluating XSOAR in competitive processes consistently cite deployment complexity and the maintenance burden of playbook libraries that break when upstream log formats or tool APIs change. AgentiX addresses some of this, but it remains in early availability as of late 2025. The platform still operates over whatever alerts the detection layer surfaces, which means coverage gaps upstream propagate through every automated workflow downstream.
Buyer fit: Large enterprises with established Palo Alto Networks deployments that want tight ecosystem integration and are willing to invest in a complex playbook environment.
D3 Security's Morpheus AI platform investigates and triages 100% of incoming security alerts in under three minutes using a purpose-built cybersecurity LLM. The stack-agnostic deployment model sits on top of existing security tooling, and the emphasis on evidence collection and compliance reporting addresses requirements that pure SOC-triage platforms often underserve. MSSP-friendly onboarding makes it accessible for service providers managing multiple client environments.
D3 operates at the alert and case management layer. The compliance evidence collection use case is well-served, but the platform's value is bounded by the quality and completeness of alerts flowing into it. Three-minute triage is fast, but speed doesn't compensate for alerts that never fire because the log source was excluded from monitoring.
Buyer fit: Organizations where case management, evidence collection, and compliance reporting are primary automation priorities alongside alert triage.
Every platform above automates over whatever data the existing security stack can see. Strike48 addresses the data foundation first.
The federated search architecture queries logs in their existing stores without requiring upfront parsing or schema decisions, making complete log coverage economically viable. Search-in-place connectors hit existing S3, Splunk, or Elastic stores without migration. No duplicate storage costs. No forced cutover. SOC teams receive an average of 2,992 security alerts per day, and most of those fire against a partial picture of the environment. Federated search makes the full picture queryable because logs stay in their native stores at raw storage cost, and parsing happens only against what agents request at query time.
The agent architecture diverges most clearly from workflow-based platforms. Rather than a monolithic AI handling all tasks through a broad prompt, Strike48 breaks the work into narrowly scoped micro agents. A coordinator agent splits the investigation; specialist agents handle correlation, forensic collection, and evidence synthesis; results route back to the coordinator. Narrow scope is the anti-hallucination mechanism. GraphRAG persona and knowledge graphs constrain what each agent knows. MCP connectors constrain what tools it can invoke. Agents given small, specific jobs don't hallucinate to please you because they reason from defined context rather than statistical approximation.
Pre-built agent packages (SOC Level 1, SOC Level 2, phishing detection, fraud detection, compliance evidence collection) deploy without custom development. Prospector Studio lets teams build custom agents without dedicated AI engineering resources, with documented use cases showing analysts saving 30 minutes per day on query building and report generation alone. Mean time to detection dropped below eight minutes in early deployments.
Buyer fit: Organizations where log coverage gaps are a known, unsolved problem. Security teams that have tried AI-assisted tools and found outputs degraded by incomplete data. Enterprises that want to extend agentic workflows beyond SOC triage into fraud detection, compliance automation, and IT incident response without adding another vendor.
Four dimensions separate these platforms in ways that matter operationally.
The data foundation column determines whether any AI or agentic capability downstream can be trusted. Every platform that inherits existing gaps automates the alerts it can see. Whether that covers the full environment is a question each team needs to answer before selecting a platform. If the answer is "we monitor roughly two-thirds of our log sources," then faster automation over two-thirds coverage still leaves one-third of the attack surface uninvestigated.
Different problems point to different answers.
If the problem is workflow flexibility across teams (security, IT, HR, operations), Tines remains a strong answer. No platform in this list matches its cross-functional breadth.
If the problem is that existing SOAR or workflow automation runs over incomplete data and the SOC still can't reduce analyst load or mean time to detection, the answer is a data foundation upgrade paired with purpose-built agents. Torq and Swimlane are reasonable evolutionary steps for teams with mature SIEM coverage. Strike48 is the option when full log coverage and agentic intelligence are both requirements.
If the problem is transitioning away from Splunk SOAR or Cortex XSOAR specifically, the first question is whether the goal is to maintain existing log infrastructure or fix the coverage layer at the same time. Maintaining the log layer while upgrading the automation layer points to Torq or Swimlane. Fixing both simultaneously points to Strike48.
The question is which platform can act on complete data without creating human bottlenecks at every investigation step. That leads to a shorter list.
If that analysis points toward agentic intelligence over complete log coverage, see what the data foundation plus purpose-built agents actually look like in practice. Request a demo.
Q: Who does Tines compete with? A: Tines competes with SOAR platforms (Splunk SOAR, Cortex XSOAR, Swimlane), AI SOC platforms (Torq, D3 Security), and agentic log intelligence platforms (Strike48). The relevant comparison depends on whether you're evaluating general workflow automation across business functions or security-specific agentic operations with deep log intelligence.
Q: Is Tines a SOAR platform? A: Tines is often evaluated alongside SOAR platforms but positions itself as a broader workflow automation tool. It lacks some of the security-specific case management, pre-built security playbook libraries, and detection-layer integrations that purpose-built SOAR platforms provide natively. For teams that need deep SOC-specific agent behaviors or compliance evidence collection out of the box, dedicated security platforms cover more without requiring custom builds.
Q: How big is Tines? A: Tines is a security automation company founded in 2018 and headquartered in Dublin, Ireland. The company raised $125M in Series C funding in February 2025, bringing total funding to $272M and valuation to $1.125B. Investors include Goldman Sachs, SoftBank Vision Fund, and CrowdStrike.
Q: Is Tines a good company? A: Tines earns consistently strong user reviews (4.8 stars on G2, 4.9 on Gartner Peer Insights) and was named a Gartner Peer Insights Customers' Choice for SOAR in 2025. Its reputation is strongest among teams that need cross-functional workflow automation. Whether it's the right fit depends on whether workflow flexibility or log-grounded agentic security is the primary requirement.