
SOAR's pitch was clean. Automate incident response through playbook-driven orchestration. Let security teams handle more alerts without adding headcount. The economics looked simple. Implementation proved otherwise.
The failure mode is maintenance. Every new log source, every schema change, every edge case needs a playbook update. Engineers who were supposed to investigate threats write if-then logic instead. The tool built to reduce analyst burden created an engineering burden that scales with environment complexity. Teams running 300 or more playbooks spend 20 to 40 hours a month on maintenance alone, and that number grows every time the environment changes.
This is architectural, not vendor-specific. Deterministic playbooks can't reason through novel alerts. Attacks don't arrive formatted for a decision tree written six months ago. When a pattern deviates, playbook automation produces false negatives or misrouted escalations. Alerts get dropped. Wrong analysts get wrong context. Both outcomes compound. The SOC never learns what it missed because the playbook can't flag what it wasn't built to recognize.
Is playbook-based automation the right model for environments where alert types, log formats, and attack patterns change faster than engineers can write rules?
Three criteria separate genuine architectural improvements from SOAR with a new interface.
Adaptive investigation over static playbooks. Can the alternative reason through alerts it has never seen before? A platform that executes predetermined steps and one that forms a hypothesis, gathers evidence, and reaches a conclusion on a novel alert type represent fundamentally different architectural models. The vendor test question: "Show me how your platform handles an alert type that isn't in your existing playbook or training data library."
Log visibility scope. Does the alternative operate across the full log environment, or does it inherit the visibility gaps of whatever SIEM feeds it? IDC research indicates the average enterprise monitors only about two-thirds of its environment due to log storage economics. An alternative that fires against that partial coverage faster still leaves every unmonitored log source as a potential attack path generating zero alerts and zero investigations, regardless of how capable the investigation layer is.
Audit trail completeness. Does the platform maintain a verifiable, step-by-step record of every agent or automation decision, including why it reached a conclusion? Teams that cannot show auditors exactly what automated systems did and why face the same accountability gap as teams with no automation at all. For regulated industries, the audit trail is not optional. SOC 2 and equivalent frameworks require documented evidence of how automated systems reached each decision.
TLDR: For teams where playbook maintenance is the bottleneck and log coverage is already mature, agentic platforms like Dropzone AI or hyperautomation tools like Torq represent real improvements over legacy SOAR. For teams where log coverage gaps are the root problem (because agents reasoning over incomplete data produce confident but unreliable conclusions), Strike48 is the only alternative in this comparison that addresses both the data foundation and the automation layer in a single platform.
Key Takeaways:
These platforms were designed from the start without a playbook dependency. They investigate alerts adaptively rather than executing predetermined steps. Strongest fit for teams where investigation depth and alert novelty are the primary challenges.

Overview
Dropzone AI builds autonomous alert investigation workflows. The platform analyzes alerts, correlates evidence across connected data sources, and returns investigation conclusions without requiring analysts in the loop for routine triage. Instead of executing a predetermined response workflow, Dropzone AI investigates the way a senior Tier 2 analyst would, adapting its approach to the specific alert context.
What you need to know about Dropzone AI
Investigation quality is bounded by the alert stream feeding it. If the underlying SIEM or detection tooling covers only a portion of the environment, Dropzone AI produces high-fidelity analysis of alerts that exist while threats in unmonitored log sources generate no alerts at all. The platform does not address log coverage gaps upstream. It’s a clear-eyed architectural tradeoff. The investigation tool is excellent, but it’s bounded by the data foundation beneath it. Dropzone AI suits security teams with a mature, well-funded SIEM who want to reduce analyst load on investigation without changing data infrastructure, along with MSSPs scaling investigation capacity across client environments where complete log coverage is already in place.
Key takeaways:

Overview
Simbian is an agentic AI SOC platform that runs autonomous security operations across alert triage, threat detection, and incident response. Agents take actions on security events rather than surfacing recommendations for human execution. Legacy SOAR executes playbooks. AI-assisted SOAR recommends the next playbook step. Simbian agents reason through the investigation and act on conclusions, reducing the number of alert-handling steps that require a human decision.
What you need to know about Simbian
Like other agentic platforms, Simbian’s effectiveness depends on the completeness of the data sources it connects to. Agentic reasoning over partial log coverage produces confident conclusions about an incomplete picture. No platform in this category natively addresses the economics of log storage that cause teams to monitor less than their full environment. Agents are only as reliable as the visibility beneath them. Simbian suits security teams evaluating a full replacement for playbook-driven SOAR who want agentic investigation deployed against their existing security data stack, particularly those that have moved past alert volume problems and now face investigation quality problems on novel threat patterns.
Key takeaways:
These platforms replace SOAR's playbook model with flexible API-driven workflow automation that spans more of the tool stack and requires less engineering overhead to maintain. The tradeoff is breadth over depth: they are general-purpose automation engines, not purpose-built SOC investigation tools.

Overview
Torq is a hyperautomation platform with an AI layer (the Socrates engine) that handles natural-language remediation queries and autonomous workflow generation. The platform earns its enterprise position through a wide integration ecosystem, audit trails with manual override controls, and a no-code workflow builder that lowers the barrier to automation compared with legacy SOAR requiring dedicated security engineers for every playbook change.
What you need to know about Torq
Torq automates over whatever log coverage and alert stream already exists. There is no data-layer mechanism in the Torq architecture for addressing log visibility gaps. For teams where the underlying SIEM covers only a fraction of the environment, faster orchestration over that partial coverage does not close the attack surface the unmonitored sources represent. Torq is excellent at what it does. What it does assumes the data problem is already solved. Torq suits organizations with mature SIEM infrastructure that want to replace brittle playbooks with flexible API-driven orchestration, and teams that need automation spanning beyond the SOC into IT, DevOps, or compliance workflows where a security-specialist tool would be too narrow.
Key takeaways:
Overview
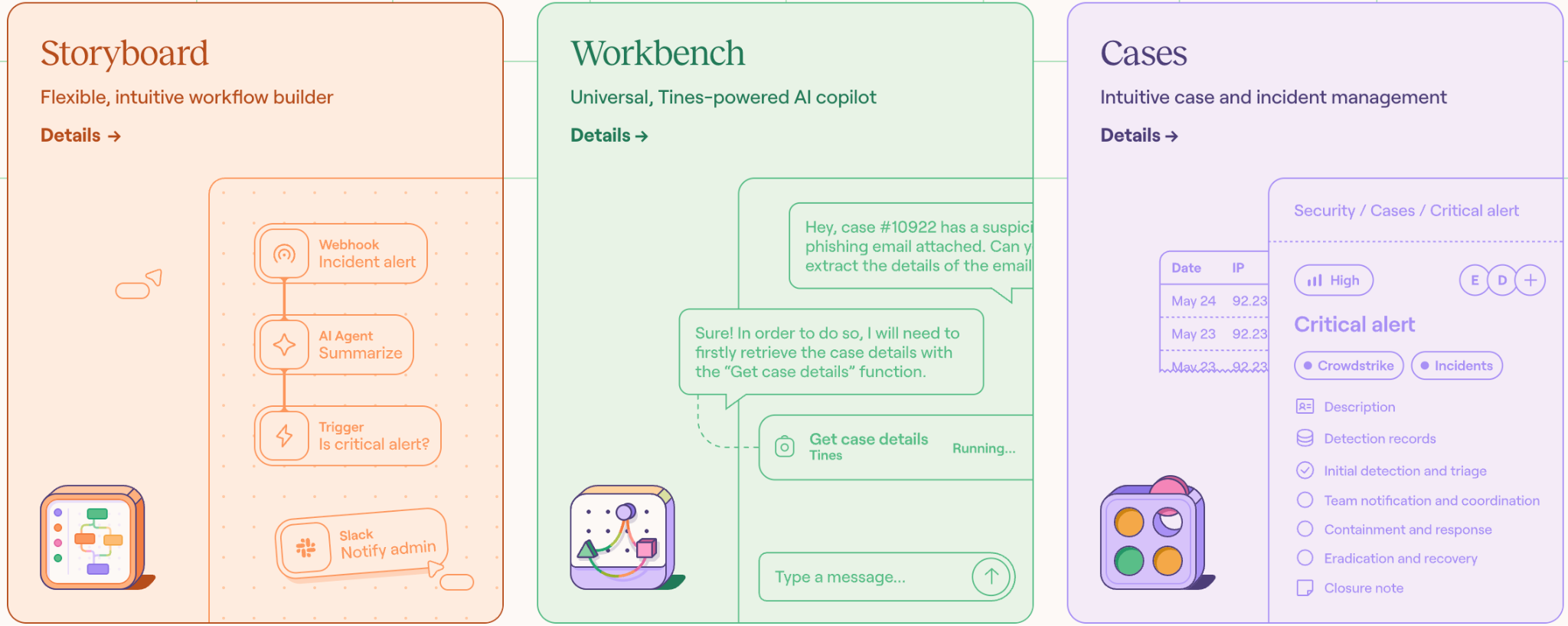
Tines is an intelligent workflow automation platform that spans security, IT, and general enterprise operations. The platform earns high practitioner ratings (4.8 stars on G2 across 200 or more reviews) through flexibility, a no-code storyboard builder that eliminates the scripting and SQL knowledge legacy SOAR required, a broad integration library, and faster workflow creation than traditional playbook authoring. Tines is a more flexible alternative to the rigid playbook model rather than a direct SOAR replacement in the traditional category sense. Teams build and modify automation workflows without dedicated security engineering resources and extend those workflows into business functions beyond the SOC.
What you need to know about Tines
Security is one vertical among many for Tines. The platform does not have native capabilities in log intelligence, SOC-specific investigation behaviors, or the data architecture decisions that determine whether AI agents have complete data to reason from. Teams that want purpose-built agent intelligence grounded in log data will find Tines built wide rather than deep on security-specific use cases. Tines suits security teams sharing tooling with IT and other business functions that want consistent automation across the organization, and teams already running Tines that want to add AI capabilities incrementally rather than migrating to a new platform.
Key takeaways:
These platforms add AI capabilities on top of existing playbook architectures. They offer an evolutionary path for teams with existing playbook investments and provide a lower switching cost than architectural replacement. The underlying logic remains deterministic. AI reduces friction within that model rather than replacing it.

Overview
Cortex XSOAR (Palo Alto Networks) is one of the most widely deployed SOAR platforms in enterprise security. The platform holds that position through an extensive playbook library, deep integrations across the security stack, a mature case management layer, and enterprise support infrastructure. AI additions assist with playbook recommendations, alert triage, and investigation summaries. For teams with established SOAR deployments, dedicated security engineering resources, and years of playbook investment, the depth and Palo Alto ecosystem integration reduce the risk of full architectural replacement.
What you need to know about Cortex XSOAR
The AI capabilities are layered on a fundamentally playbook-based engine. AI assists playbook execution. It does not replace the playbook model. Novel alerts outside existing playbook coverage still require manual playbook authoring. The maintenance burden that drove teams to evaluate alternatives persists, and teams still spend those 20 to 40 engineering hours per month updating playbooks as their environment changes.
That is the defining tradeoff of next-gen SOAR as a category. AI reduces friction within the existing model without resolving whether the model itself is the right architecture for today’s threat environment. Cortex XSOAR suits large enterprises with established SOAR deployments, mature playbook libraries, and security engineering teams experienced with playbook maintenance, especially organizations where the switching cost of full SOAR replacement outweighs the benefits of moving to an agentic architecture.
Key takeaways:
Overview
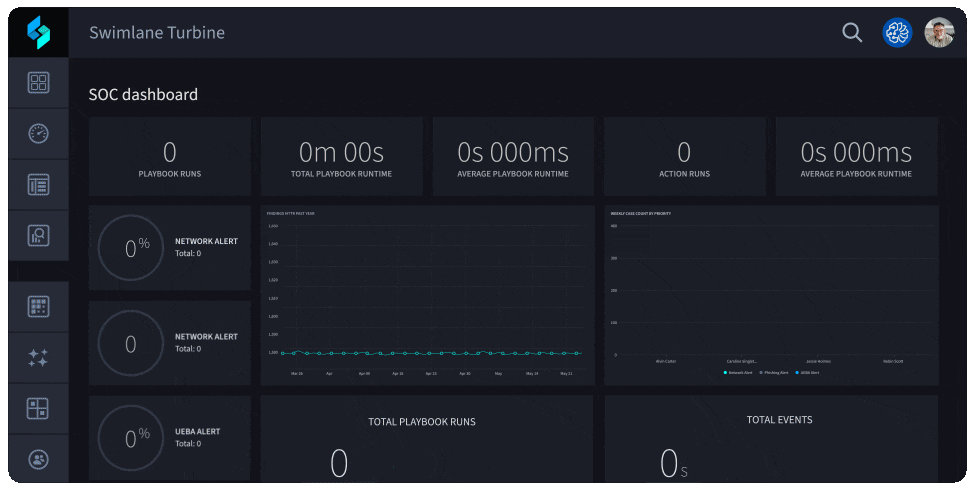
Swimlane Turbine is a low-code SOAR platform with AI-assisted automation capabilities. The platform differentiates within its category through a low-code workflow builder that cuts playbook creation time to a fraction of what legacy SOAR engineering required, AI features that assist with anomaly detection and alert triage, and a cloud-native architecture that improves on legacy on-premises SOAR deployment models. For teams that have struggled with SOAR’s engineering overhead rather than its architectural model, Turbine offers a measurable reduction in maintenance friction while preserving playbook investment.
What you need to know about Swimlane Turbine
Like Cortex XSOAR, Turbine’s automation model is fundamentally playbook-based with AI layered on top. Low-code tooling makes playbook updates faster, but the dependency on predefined workflow logic remains. Alert types outside playbook coverage still require human intervention or new playbook authoring. Low-code SOAR addresses the maintenance burden. The investigation logic problem (reasoning through novel alerts without a predetermined decision tree) remains unsolved. Turbine suits mid-market security teams that want a modernized SOAR with less engineering overhead than legacy platforms, and organizations transitioning from on-premises SOAR that need a cloud-native alternative preserving existing playbook logic while reducing per-change engineering cost.
Key takeaways:
Overview
Strike48 solves the problem that none of the other categories address: the completeness of the data that agents and automation reason over. Every category covered so far automates or investigates over whatever log data already exists. Every platform's effectiveness is bounded by the completeness of the underlying log environment. IDC research indicates the average enterprise monitors only about two-thirds of its environment due to log storage economics. For organizations in that majority, replacing SOAR with a better orchestration or investigation tool accelerates operations within a structurally incomplete picture. That is the second evaluation criterion from earlier in this article, and most alternatives cannot address it.
What you need to know about Strike48
Strike48 addresses the data foundation before deploying agents. Search-in-place connectors for S3, Splunk, Elastic, and existing data stores deliver full log coverage without migrating data or paying to store the same log twice. AI-assisted collectors cover approximately 80% of log sources in under a day. The result: 100% coverage becomes economically viable rather than aspirational, and teams stop making coverage decisions based on budget rather than risk.
On top of that complete data layer, Strike48 deploys narrowly scoped micro-agents, each with a specific job, a defined knowledge graph via GraphRAG, and constrained tool access via MCP connectors. Agents hand work off to each other like a coordinated SOC team. The narrow scope is deliberate: agents given small, specific jobs don't hallucinate to please you. GraphRAG persona graphs define what each agent knows, and MCP tool constraints restrict what each agent can do, so investigation outputs reflect the actual environment rather than statistical approximation. This architecture addresses all three evaluation criteria from earlier: adaptive investigation (agents reason through novel alerts without predetermined playbooks), log visibility scope (federated search provides the complete data foundation), and audit trail completeness (every agent step is deterministic and traceable).
The operational results reflect the architectural difference. Mean time to detection dropped below eight minutes in early deployments. Strike48 agents uncovered active phishing campaigns that legacy tools had missed and generated validated detection rules before real attacks occurred. Prospector Studio compresses 30 minutes of daily analyst work into seconds. Teams that moved to Strike48 stopped maintaining playbooks and started investigating threats that were previously invisible.
Key takeaways:
Each team's environment and priorities determine which tradeoffs are acceptable. Use this table as a decision tool, not a ranking.
Replacing SOAR requires more than choosing a better playbook engine. The structural problem is that deterministic playbooks cannot scale to environments where alert types, log formats, and attack patterns change faster than engineers can write rules. Most SOAR alternatives solve this by swapping the playbook model for adaptive investigation. That is a genuine improvement worth making.
The second problem is harder. Adaptive investigation over incomplete log coverage produces better-reasoned conclusions about a partial picture. The question worth asking before selecting any platform in this comparison: what percentage of your environment does the data feeding that AI actually see? Most vendors here cannot answer that for their customers because they do not own the data layer.
For teams where log coverage is already mature, the agentic and hyperautomation alternatives in this article represent real options for escaping SOAR's maintenance burden. For teams where coverage gaps are a known, unresolved problem, the data foundation comes before the automation layer. Solving for speed on top of incomplete visibility is not a security outcome.
See what complete visibility plus purpose-built agents looks like. Request a demo of Strike48 .
Q: Is SOAR outdated? A: SOAR's core architectural model (deterministic playbook execution) is showing structural limits in environments that change faster than playbooks can be maintained. The category is splitting into next-gen SOAR (AI added to playbooks) and agentic platforms (playbooks replaced entirely). Whether SOAR is outdated depends on which problem your team faces most acutely: playbook maintenance overhead or investigation quality on novel alerts.
Q: How does SOAR compare to SIEM? A: SIEM collects, normalizes, and stores log data. SOAR orchestrates automated responses to SIEM-generated alerts. They address different layers of the security stack: visibility versus response. Most SOAR alternatives, including agentic platforms, depend on SIEM data the same way traditional SOAR does. The exception is platforms like Strike48 that include their own data foundation layer and can query logs where they already live.
Q: Does Splunk have a SOAR product? A: Splunk SOAR (formerly Phantom) is a dedicated SOAR product within the Splunk portfolio, distinct from Splunk's SIEM capabilities. Teams using Splunk as their SIEM can connect most SOAR alternatives to it via search-in-place connectors or standard API integration. Splunk SOAR is not the only automation option for Splunk environments.
Q: What makes an agentic SOC different from SOAR with AI features? A: The distinction is architectural. SOAR with AI features still executes predefined workflows; AI assists the execution or recommends the next step. An agentic SOC deploys agents that reason through alerts autonomously, form hypotheses, gather evidence, and reach conclusions without a predetermined decision tree. The failure mode of SOAR-with-AI is playbook coverage gaps. The failure mode of an agentic SOC is data quality gaps. The choice of which failure mode to accept should depend on which problem your team faces more acutely and which data foundation already exists.